July 03, 2018
Credential Re-Use in the Enterprise
Written by
Justin Bollinger
Password Audits
Penetration Testing
Program Assessment & Compliance

 Many of our customers follow the best practice of creating separate accounts for day-to-day tasks and administrative ones. In the event of an attack, using separate accounts is often a great way to slow things down and give security teams a little extra time for discovery and identification of an attack. Because many attacks happen in the user context, this creates an extra step for an attacker, who must escalate the privileges to administrative permissions.
Unfortunately, something I have discovered on a number of engagements is that users don’t like to remember multiple passwords. Many users just set the same password for both accounts. This practice circumvents the whole purpose of having separate accounts.
Many of our customers follow the best practice of creating separate accounts for day-to-day tasks and administrative ones. In the event of an attack, using separate accounts is often a great way to slow things down and give security teams a little extra time for discovery and identification of an attack. Because many attacks happen in the user context, this creates an extra step for an attacker, who must escalate the privileges to administrative permissions.
Unfortunately, something I have discovered on a number of engagements is that users don’t like to remember multiple passwords. Many users just set the same password for both accounts. This practice circumvents the whole purpose of having separate accounts.
 Many organizations even make it easy for an attacker to identify these accounts by using “tags” in the naming convention to designate if the user is administrative or not. For example, the user John Smith’s regular account may be jsmith, while the administrative account assigned to John may be jsmith-adm. When escalating privileges during a penetration test, I often have success by simply trying the known password against the “paired” administrative account.
One additional step that I’ll take during a penetration test is after compromising an Active Directory domain, I’ll take the extracted hashes and run them against a script to identify accounts that share the same password. Including this information in a report can give valuable insight to organizations, which often leads to updating end-user training.
https://gist.github.com/bandrel/3dd47c93cd430606865ec84d281913dc
To use the script, just add the file to be checked as an argument. The script will output groups of users that share the same password.
Many organizations even make it easy for an attacker to identify these accounts by using “tags” in the naming convention to designate if the user is administrative or not. For example, the user John Smith’s regular account may be jsmith, while the administrative account assigned to John may be jsmith-adm. When escalating privileges during a penetration test, I often have success by simply trying the known password against the “paired” administrative account.
One additional step that I’ll take during a penetration test is after compromising an Active Directory domain, I’ll take the extracted hashes and run them against a script to identify accounts that share the same password. Including this information in a report can give valuable insight to organizations, which often leads to updating end-user training.
https://gist.github.com/bandrel/3dd47c93cd430606865ec84d281913dc
To use the script, just add the file to be checked as an argument. The script will output groups of users that share the same password.
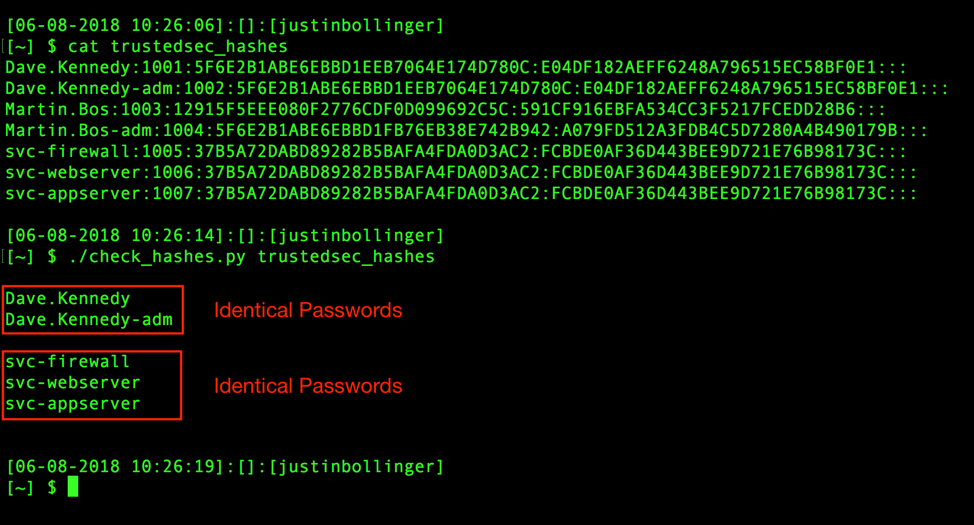 C’mon Dave, you know better than that. Guess we’re going to have to send you back to training!
C’mon Dave, you know better than that. Guess we’re going to have to send you back to training!