Critical Exposure in Citrix ADC (NetScaler) – Unauthenticated Remote Code Execution

On December 17, 2019, Citrix released a critical advisory that allows for remote code execution. Advisories like these come out often for organizations, and critical exposures are nothing new for any company. However, when digging into the remediation step details, this advisory gave a substantial amount of information on the exploit itself. What makes this substantially worse is that there is no direct patch for this issue. Citrix has released mitigation steps for CVE-2019-19781, which requires a number of direct commands through the interface to address the issue.
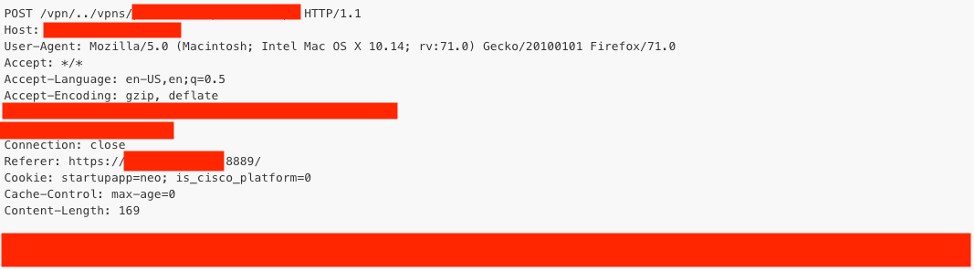
TrustedSec can confirm that we have a 100% fully working remote code execution exploit that is able to directly attack any Citrix ADC server from an unauthenticated manner. Based on the information already provided in the workaround, the exploit itself was relatively trivial and allows for the ability to compromise the underlying operating system. The exposure is contained within a vulnerable parameter that allows for directory traversal and the ability to call poorly written scripts.
It is advised that anyone leveraging Citrix ADC (NetScalers) should follow the links at the bottom of this post (specifically, the mitigation efforts to address this vulnerability) immediately. We are aware of large scanning efforts already occurring across the globe in an effort to map NetScalers for this specific vulnerability and exposure.
The workarounds are focused on eliminating directory traversals in general and restricting access to the VPNs folder, which contains scripts that allow files to be written (in a specific format) to later be called for remote code execution.
add responder policy ctx267027 "HTTP.REQ.URL.DECODE_USING_TEXT_MODE.CONTAINS(\"/vpns/\") && (!CLIENT.SSLVPN.IS_SSLVPN || HTTP.REQ.URL.DECODE_USING_TEXT_MODE.CONTAINS(\"/../\"))" respondwith403
Impacted Systems:
- Citrix ADC and Citrix Gateway version 13.0 all supported builds
- Citrix ADC and NetScaler Gateway version 12.1 all supported builds
- Citrix ADC and NetScaler Gateway version 12.0 all supported builds
- Citrix ADC and NetScaler Gateway version 11.1 all supported builds
- Citrix NetScaler ADC and NetScaler Gateway version 10.5 all supported builds
Supporting Links:
https://support.citrix.com/article/CTX267027
https://support.citrix.com/article/CTX267679
https://nvd.nist.gov/vuln/detail/CVE-2019-19781#vulnCurrentDescriptionTitle