CVE-2020-2021: PAN-OS SAML Security Bypass

On June 29, 2020, Palo Alto released information on a Security Assertion Markup Language (SAML) authentication bypass CVE-2020-2021. Palo Alto published the advisory PAN-148988 for a critical issue affecting multiple versions of PAN-OS.
An Overview of the Vulnerability
Description:
With network access to a device running a vulnerable version of PAN-OS and configured to use Security Assertion Markup Language (SAML) authentication, an unauthenticated remote attacker can abuse improper verification of SAML signatures to bypass authentication and subsequently gain access to resources that otherwise would have been protected. While multiple Palo Alto devices are impacted by CVE-2020-2021, vulnerable edge devices such as GlobalProtect VPNs are at the highest risk for exploitation.
Our intentions are to demonstrate that this is a common configuration and a requirement for the being vulnerable @RyanLNewington does a great job explaining how SAML works here.
https://threadreaderapp.com/thread/1278074919092289537.html
Prerequisites for exploitation:
To exploit CVE-2020-2021, the PAN-OS device in question must be configured with the following options.
1. SAML Authentication Enabled
SAML authentication may be enabled in environments where SAML single sign-on is used to simplify authentication to multiple applications through an integration with an Identity Provider (IdP).
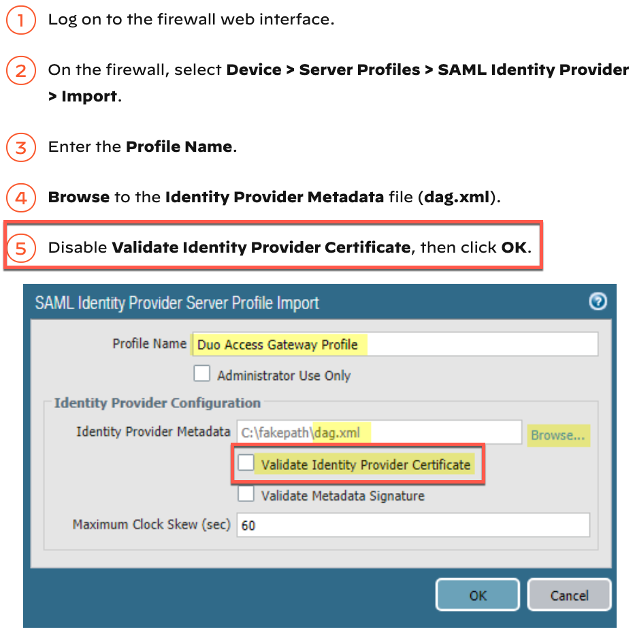
2. The “Validate Identity Provider Certificate” Option Disabled
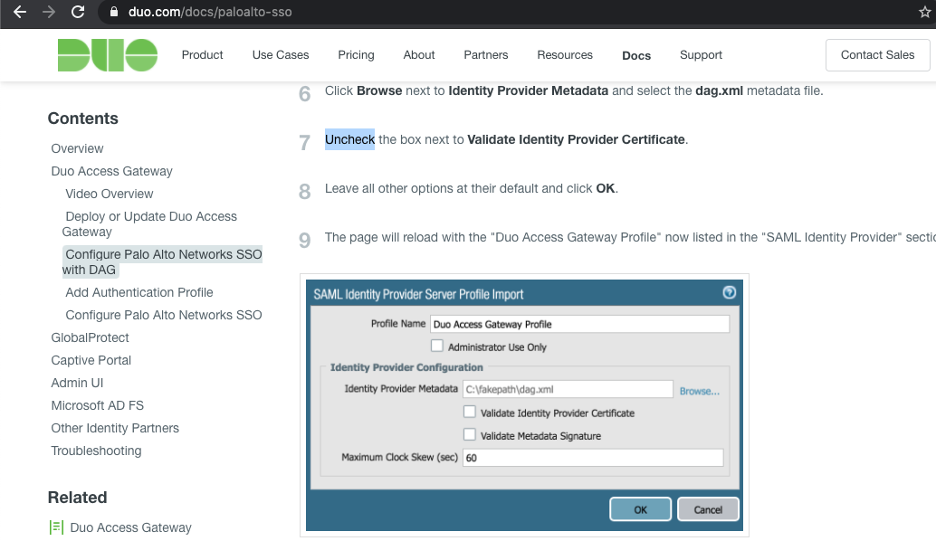
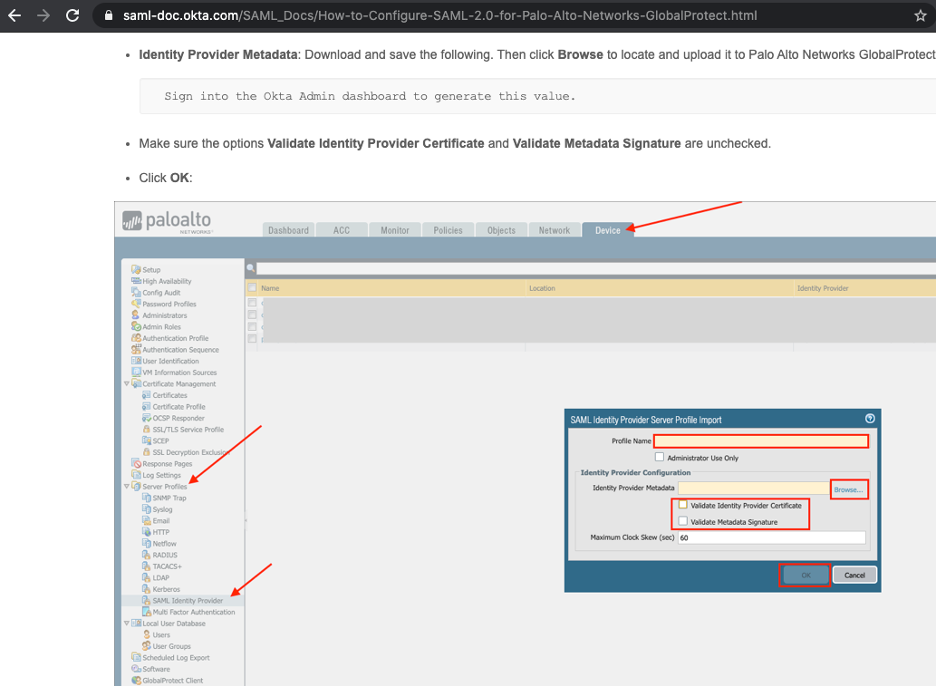
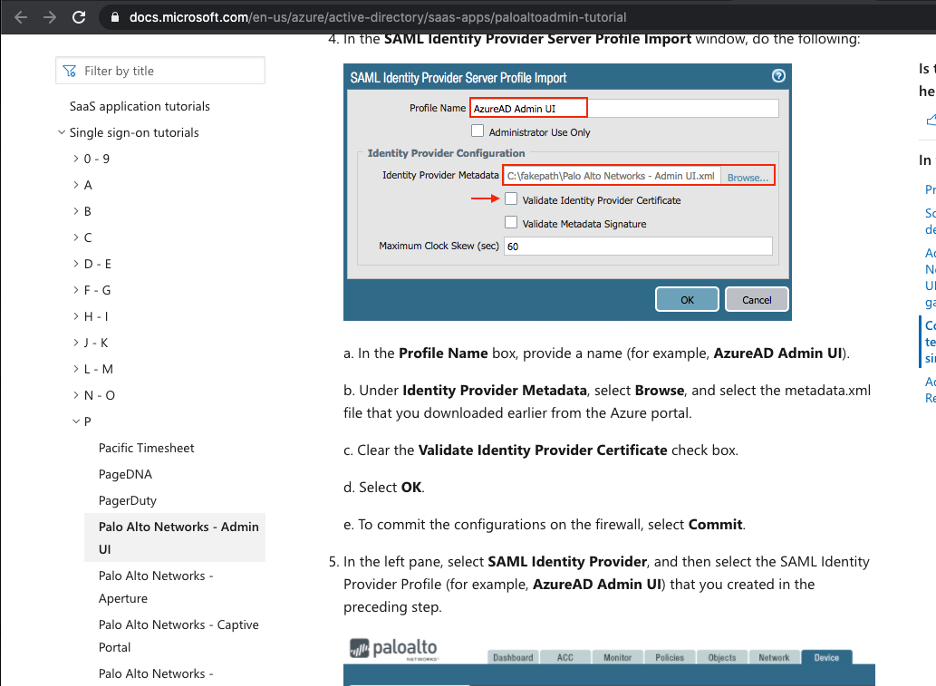
While Palo Alto requires the use of HTTPS certificates to ensure confidentiality of SAML assertions, it also includes the capability to bypass the validation of IdP certificates. In it’s documentation for the configuration of SAML authentication with PAN-OS 8.1, Palo Alto recommends that the option “Validate Identity Provider Certificate” be enabled “to ensure it (the certificate) hasn’t been compromised.” However, (similar to what was pointed out by @FrankMcG on Twitter) in their walkthrough for configuring MFA between Duo and a PAN-OS device, Palo Alto describes disabling the very same option.
A number of SAML providers also include disabling “Validate Identity Provider Certificate” in their deployment guides.
US Cyber Command is also urging timely patching based on the severity of this exposure: https://www.us-cert.gov/ncas/current-activity/2020/06/29/palo-alto-releases-security-updates-pan-os
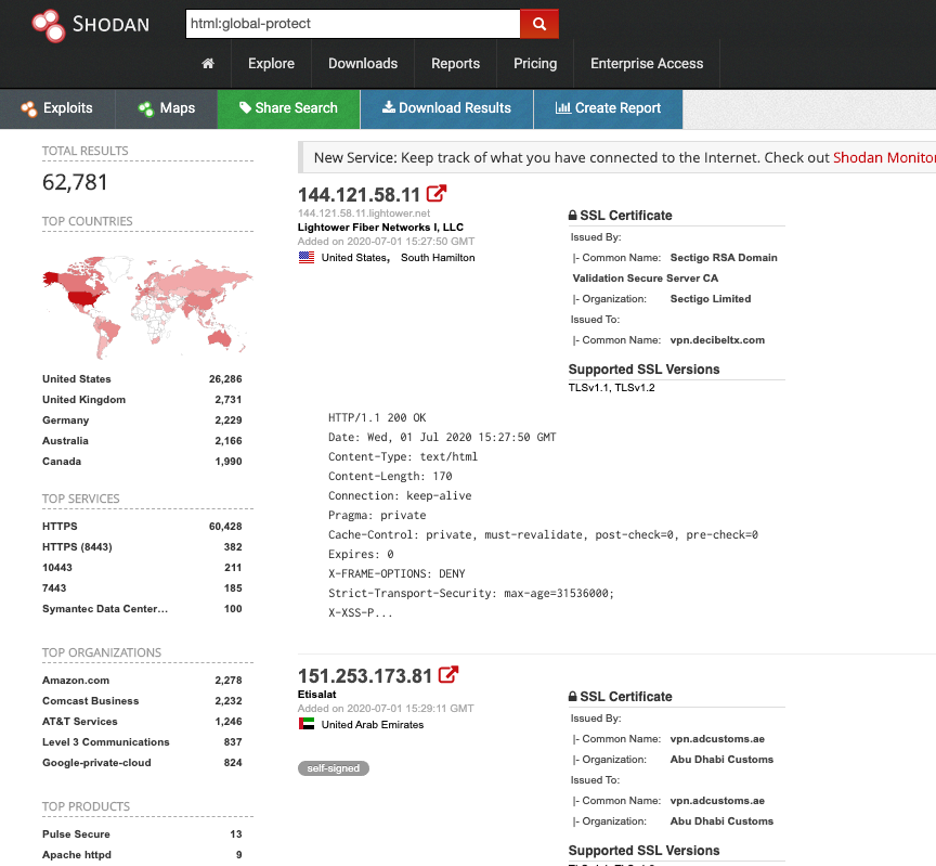
Additionally, a quick search of Shodan shows a number of potential GlobalProtect installations.
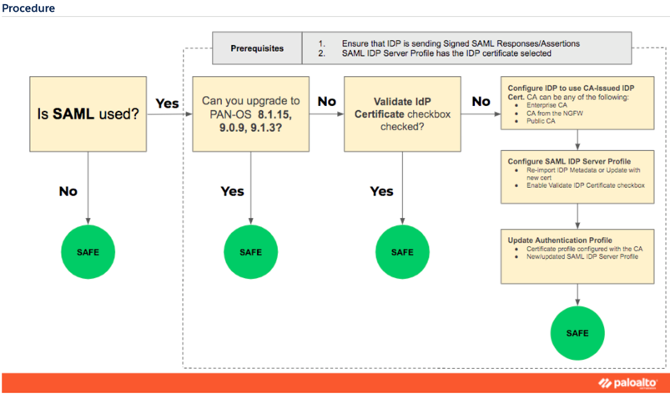
MITIGATION
Upgrade the current version of PAN-OS.
If SAML is currently in use, organizations should follow the recommended remediation guidelines:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u0000008UXK
PROOF OF CONCEPT
Currently, there is no proof of concept or example code.
DEFENSIVE MONITORING
To verify that an organization's Palo Alto appliance has been compromised, the following logs should be reviewed for Indicators of Compromise (IoCs). Organizations should look for abnormal usernames and source IP addresses that do not conform with known-good activity.
- Authentication Logs
- User-ID Logs
- ACC Network Activity Source\Destination Regions (Leveraging the Global Filter feature)
- Custom Reports
- Global Protection Logs
CONCLUSION
Currently, there is no evidence that this vulnerability has been exploited in the wild. However, the vulnerability has the potential to be a great threat to those who deploy Palo Alto equipment for remote access. TrustedSec clients should deploy the patch as soon as possible.
THE AFFECTED PAN-OS VERSIONS:
| Version | Vulnerable | Not Vulnerable |
| 9.1 | < 9.1.3 | >= 9.1.3 |
| 9.0 | < 9.0.9 | >= 9.0.9 |
| 8.1 | < 8.1.15 | |
| 8.0 | 8.0.* | |
| 7.1 | 7.1.* |
Source: https://security.paloaltonetworks.com/CVE-2020-2021
SUPPORTING LINKS:
https://security.paloaltonetworks.com/CVE-2020-2021
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-2021
https://www.us-cert.gov/ncas/current-activity/2020/06/29/palo-alto-releases-security-updates-pan-os
Complete our 5 question reader survey