Introducing SpearPhisher - A Simple Phishing Email Generation Tool

While working with clients around the globe encompassing many different lines of business with diverse environments, we frequently have to adapt as needed to conditions to complete the task at hand. Many times this requires us to custom code scripts, programs, and the like to help us automate something or to aid our clients in improving the posture of their security program. One client requested a simple and easy way to perform ad-hoc phishing email tests without requiring an outside service, a special Linux installation, or other technical requirements, with the goal being a program that a manager, director, VP, or even CIO/CSO/CISO would want to use. After reviewing the known options without finding a fitting solution, we developed SpearPhisher.
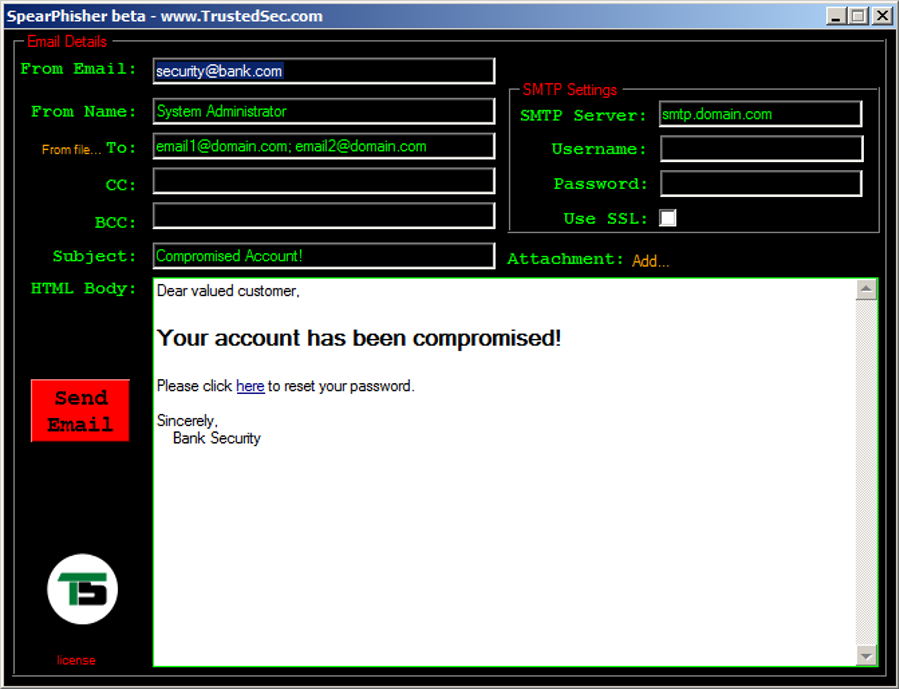
SpearPhisher is a simple point and click Windows GUI tool designed for (mostly) non-technical people who would like to supplement the education and awareness aspect of their information security program. Not only is it useful to non-technical folks, penetration testers may find it handy for sending quick and easy ad-hoc phishing emails. The tool supports specifying different sending names and email addresses, multiple recipients via TO, CC, BCC, and allows bulk loading with one recipient email address per line in a file. It allows customization of the subject, adding one attachment, and SSL support for SMTP enabled mail servers. One of the popular features with our client is the WYSIWYG HTML editor that allows virtually anyone to use the tool; previewing results as you point and click edit your malicious email body. If you want to add custom XSS exploits, client side attacks, or other payloads such as a Java Applet code generated by the Social Engineer Toolkit (SET), its split screen editor allows more advanced users to edit HTML directly.
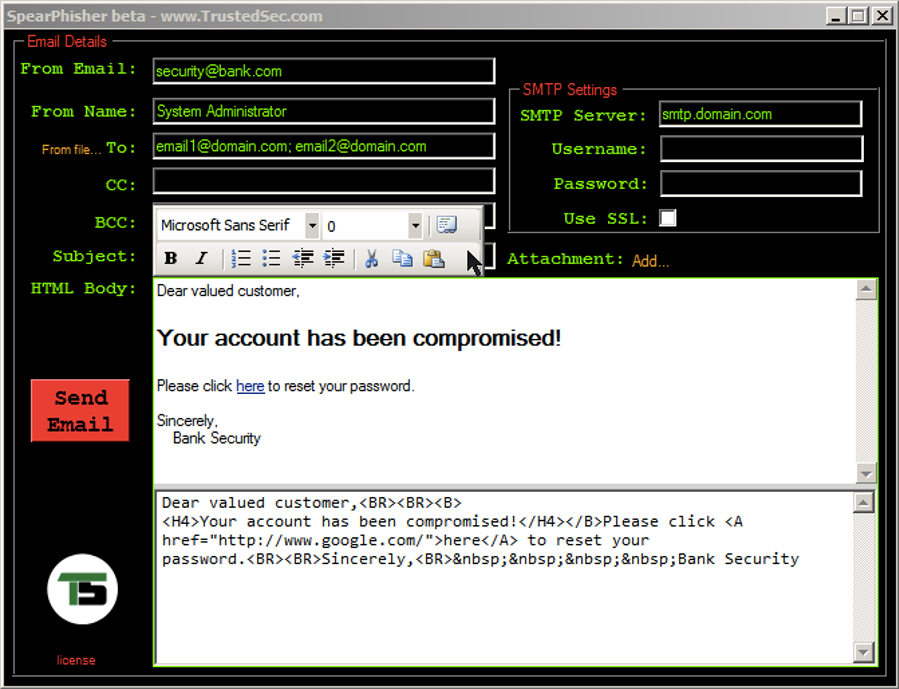
An open relay is not necessarily required as many mail servers allow authenticated users to spoof email. This is the beta release of the tool and has been tested in limited environments.