Pwnton Pack: An Unlicensed 802.11 Particle Accelerator

This past Christmas, I received a terrific gift from my in-laws: a replica Ghostbusters Proton Pack. I was thrilled. You see, growing up in the mid 80s, Ghostbusters was my jam. Fast forward 37 years and with the recent Ghostbusters: Afterlife film release, my nostalgia was hitting a fever pitch.
Shortly after our Christmas dinner, I took my kids and ventured into the dark basement to test the pack out. We were going to hunt some ghosts! After some imaginary blasting of spooks and specters, my kids passed the pack back to me and asked, "Dad, does this thing actually do anything?" Clearly, they were underwhelmed.
That question gave me an idea… let's hack it up and make it do something!
Introducing the newest entry in Wi-Fi Bustin' technology, the Pwnton Pack
Click the info buttons below to learn more!
What is this thing?!
This pack is full of wireless assessment technology capable of doing signal analysis, WPA attacks such as handshake capturing, PMKID captures, rogue access points, MitM attacks and client deauthentications, all bundled into a unique package.
Why?
Like many, I had numerous hardware and electronic devices such as Arduinos and Pis stowed away in bins that I always wanted to do something with, but never really had the time or focus to see a project through to the end. I decided to break these components out along with my collection of on-site wireless attack hardware, and started conjuring up ideas by placing displays here, attaching antennas there, and routing wires. What else does one do in the midst of a pandemic during the winter months?
Features
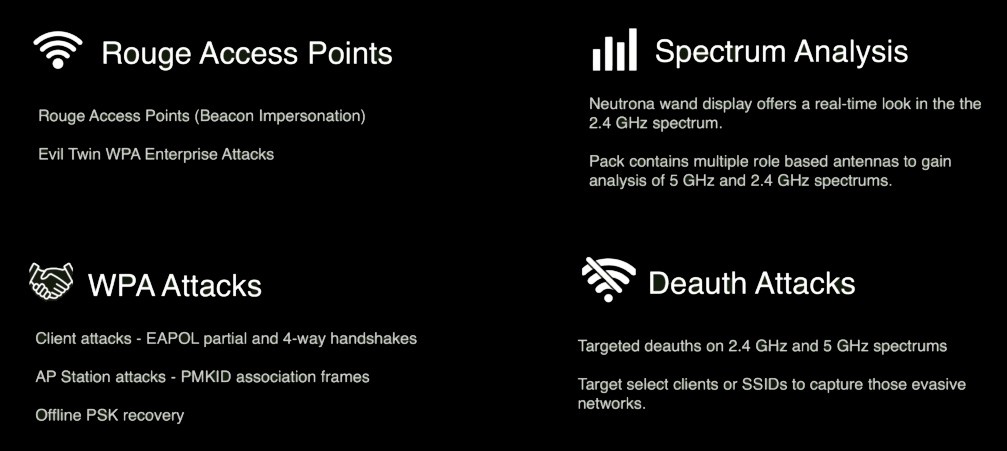
This pack features an integrated Mark VII Wi-Fi Pineapple, Raspberry Pi 4, Arduino Nano, and a proprietary ESP07 micro controller. Additionally, the pack features a proprietary light and sound kit for movie accurate effects.
Note: These are not new wireless attack techniques, nor did I create them. If these attacks are new or of interest you, I'd encourage you to take a look at the references below for more information on specific attacks.
Build
Raspberry Pi
The Pi is running a version of Pwnagotchi, an 'AI' powered by bettercap that analyzes the surrounding WiFi environment in order to gather WPA handshakes through sniffing, deauthentication, and association attacks. These handshakes (partial and full) along with PMKIDs can then be potentially recovered to derive the pre-shared keys. The Pi also gave me the ability to use external WiFi adapters that support the 5GHz spectrum.
WiFi Pineapple
The WiFi Pineapple has been a go-to device for me over the years. At the core (See what I did there?) of this compact device, the Pineapple allows for ease of managing of rogue AP attacks, such as karma-style, beacon impersonations, etc. This attack works by standing up ad-hoc access points when a WiFi device beacons out for available networks. Additionally, the Pineapple offers a modular design to add more features and tool sets, making this a perfect addition for our pack.
Micro Controllers
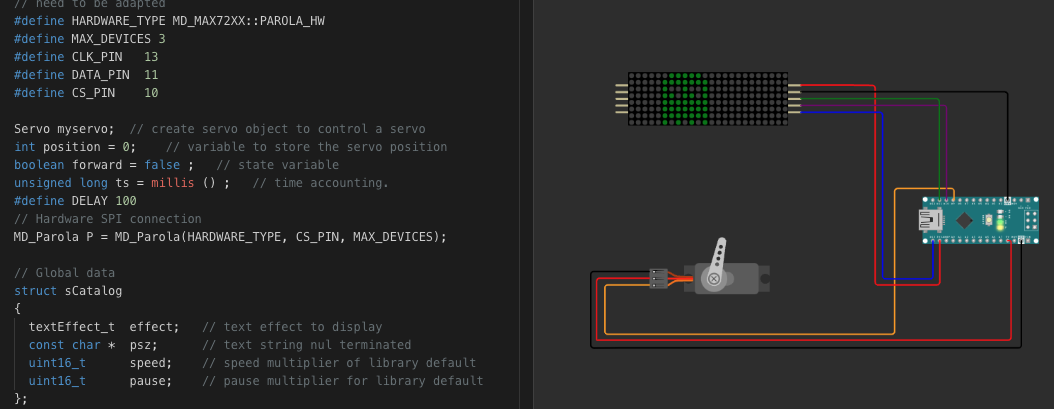
Admittedly, this project started as a way for me to get more familiar with micro controllers and some hardware hacking. It's something I've always been interested in, ever since I'd venture through security conferences watching people outfit hats to scroll text and light up.
I found that using the WOKWI website provided a great virtual lab to join components and code together for trial and error. This is where I staged the components for my Pwnton Pack. The best part of this site is that I could go from concept, testing, troubleshooting, and finished product without ever touching the soldering iron. I learned lots. It was fun to see a tangible 'thing' get created.
A particularly proud accomplishment was using Arduino's clock delays to perform multi-threading on a single-threaded processor, so the LED matrix and servo would operate simultaneously.
Neutrona Wand
The Neutrona wand features an integrated ESP07 micro controller with a tiny LED display capable of doing real-time analysis on the 2.4 GHz spectrum to find populated channels, stations, and clients. It is possible to target selected stations and clients by sending deauthentication packets using a directional yagi antenna to force wireless clients to briefly loose connection and reauthenticate to a target network. Those reauthentication handshakes are then harvested by the Pwnton Pack's antennas for off-line key recovery. The micro controller is running a wireless analysis and deauthentication suite created by SpacehuhnTech.
Power Management
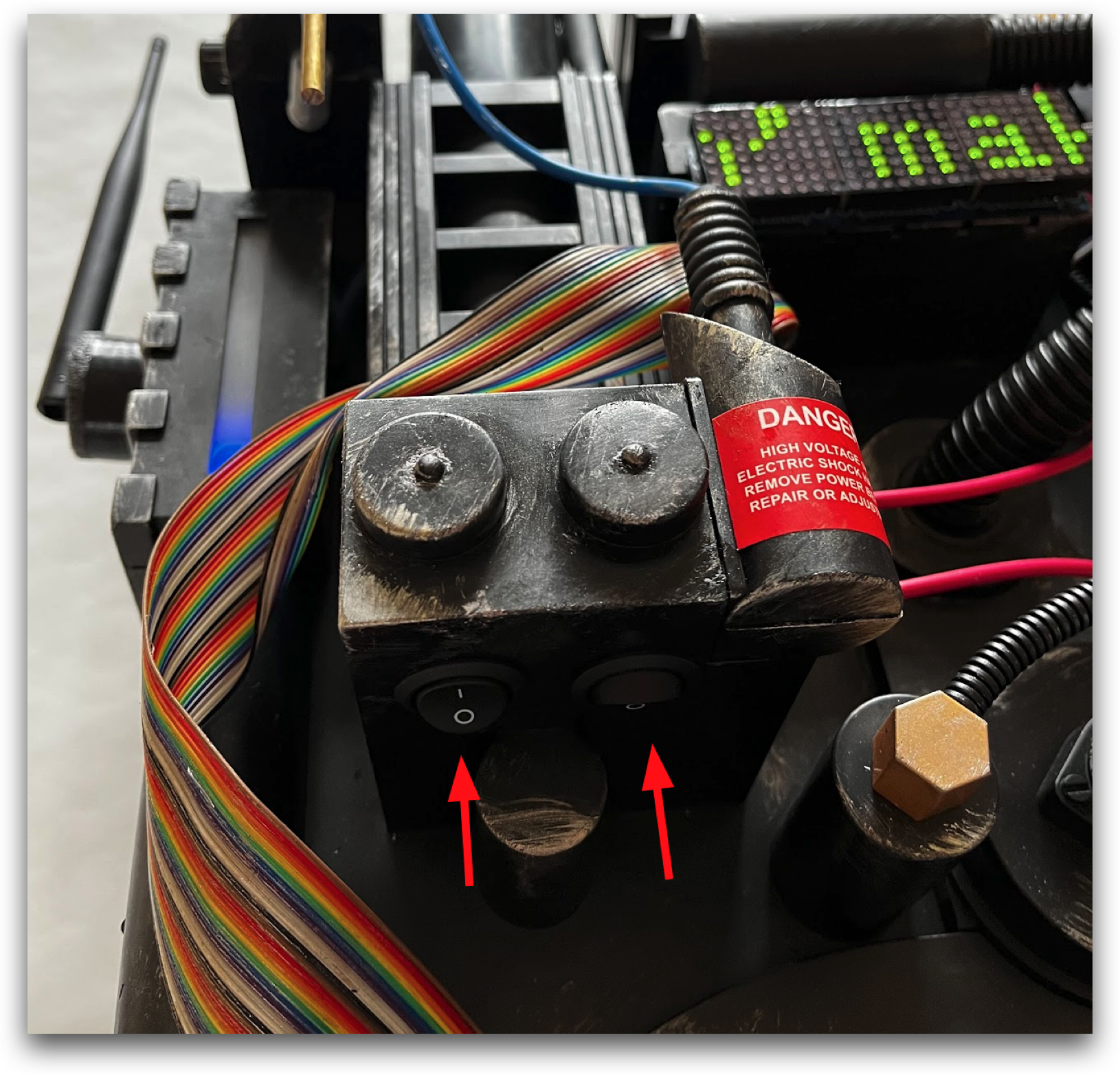
There is quite a bit going on behind the scenes with this pack for power side. The light and sound kit required a 12-volt source due to the speaker and light power draw. I picked up a lipo battery with both 12V and 5V outputs to power the sound board (12V) and Arduino (5V). A separate 5V 38800 mAh battery powers the WiFi Pineapple and Pi. These were put on three (3) independent circuits to allow individual devices to be powered on as needed, with toggle switches integrated into the pack.
Video Demonstration
Here is a video of the pack in action!
This was a wildly fun project for me. I hope it serves as a fun take on wireless security assessments and perhaps inspires others that may be new to these methods, hardware, or serve as a conversation piece at local events.
For all your wireless security assessment needs…
References
Aircrack-NG - https://www.aircrack-ng.org/
Pwnagotchi - An AI powered Bettercap WPA Handshake muncher - https://pwnagotchi.ai/
ESP07/ESP8266 Deauther - GitHub - SpacehuhnTech/esp8266_deauther: Affordable WiFi hacking platform for testing and learning
DSTIKE ESP Microcontroller - DSTIKE WiFi Deauther MiNi from Travis Lin on Tindie
WiFi Pineapple Mark VII - WiFi Pineapple - Hak5
Frankengeek Labs - Frankengeek Laboratories