Real or Fake? When Your Fraud Notice Looks Like a Phish

So I Received a Phishing Email…
I recently received an email indicating my credit card number had potentially been stolen and used for fraud. At this point, I am used to both having my credit card number stolen and receiving messages telling me it's been stolen when it has not. My attempt to determine whether I was a victim of fraud or the target of a phishing attack may help shed some light on how marketing, fraud prevention, and anyone else who sends an automated corporate email can do better.
The supposed fraud alert email I received wasn't anything special. It contained the bank's name, my full name, the last four (4) digits of my credit card number, details of a declined transaction, some links to confirm or deny the charge, and a footer with all the usual corporate boilerplate. I didn't recognize the charge, so it was time to investigate and determine if this was a legitimate email.
Is this Real or Social Engineering? The Initial Investigation
The first clue was the 'from' address. It looked like something that could belong to my bank (e.g., [email protected]) rather than a random string of letters with some sketchy domain (I'm looking at you, [email protected]). Sender addresses are ridiculously easy to forge, so this does not mean that the email is legitimate. It just means that I won't immediately relegate the message to the junk mail folder.
The next clue that lends an air of credence to this email is that it contains my full name, the last four digits of my credit card number, and claims to be from the correct bank. However, this also does not confer automatic legitimacy. The Payment Card Industry Data Security Standard (PCI DSS) rules that govern credit card security indicate that the cardholder's name and the first six (6) and last four (4) digits of a card number do not have to be encrypted or otherwise protected in any meaningful way. The issuing bank and potentially the type of card can be determined based on the first six (6) digits of the card number. This means it's entirely possible that someone who was able to get that unprotected information could craft this email, including some of my personal details, and attempt to trick me into giving them the rest of the card details or the login credentials to my account. If you think this sounds far-fetched, this exact scenario has happened to me before, albeit via a phone call rather than an email.
The next check is to hover the mouse pointer over one of the links and see where it goes without clicking on it. This is a good time to point out that I am a paranoid security professional and have my email client set to not automatically download images. This cuts down on tracking beacons, protects my eyeballs from spam that uses giant images instead of text to avoid filters, and is a hedge against a malicious email exploiting the software that decompresses and displays images (like this classic vulnerability) or any other drive-by download shenanigans. The downside is that fancy corporate email that relies on graphical buttons instead of text tends to look like a mess until I load the images. Here's what I saw in my email client when I hovered over the giant blank spot where the 'No' button should be (email addresses, account details, and tracking links have been censored to protect the innocent).
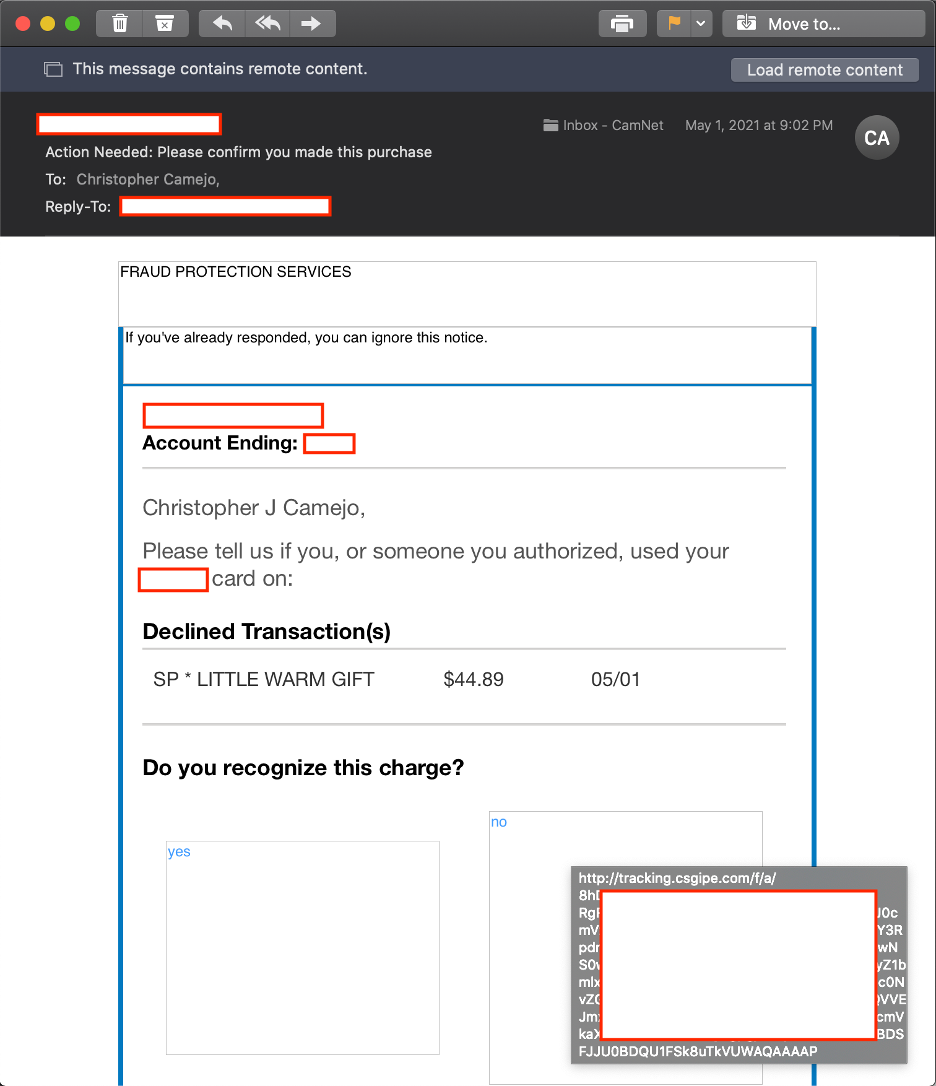
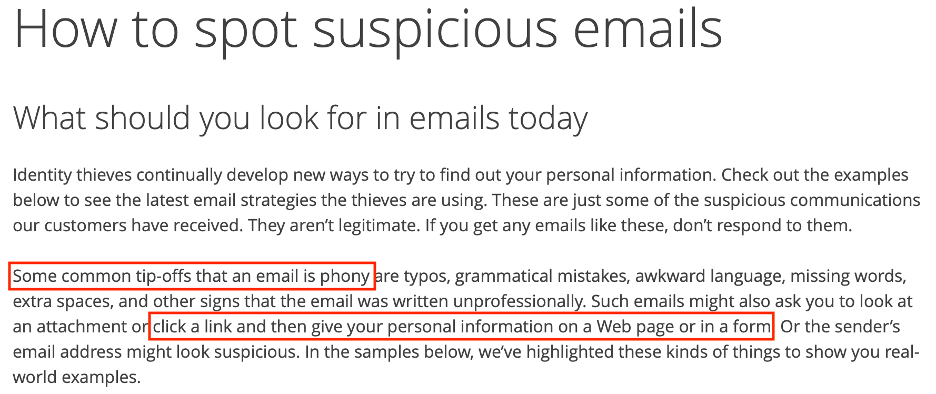
This link is a huge red flag, as it goes to tracking.csgipe.com, which isn't a domain I recognize as belonging to my bank. If a friend or relative who was less technically savvy had asked for my advice about this email, I would have considered it a targeted phishing email at this point and told them to delete it and call their bank via the phone number on the back of their credit card to report it. You don't have to take it from me, though—the bank that sent this email has a web page with instructions for spotting a suspicious email. They state that an email that asks you to click on a link and then give your personal information, which is exactly what this email was asking me to do, is a tip-off that the email is phony.
Too Legit to Quit! The Deep Dive
I'll admit, at this point I wasn't sure if this email was real or not, so it sat in my inbox for a few days. Finally, I decided that I'm a Security Professional™, so I might as well dig deeper and see what I can confirm.
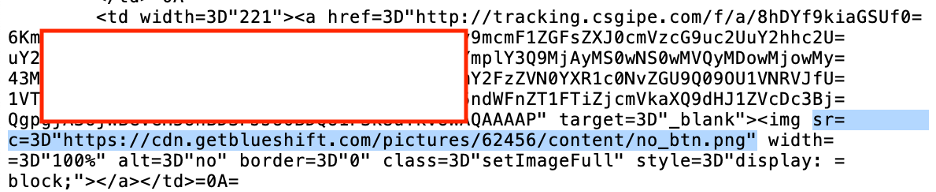
The next thing I want to check are the images, both to see if they come from one of my bank's domains and to see if they display anything that may help convince me whether the email is legitimate or not. A quick review of the email's source code reveals that every image comes from the domain cdn.getblueshift.com, which isn't a domain I recognize as belonging to my bank. So much for downloading the images! I'm not going to trust a third-party domain.
While we're rooting around in the email's source code, it's also worth looking at the headers to see what mail server it came from. At this point, it should be no surprise that I don't recognize the sending email server's domain, sparkpostmail.com, as belonging to my bank.
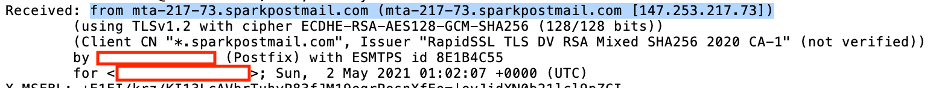
It's also worth pointing out that the headers contained a DKIM signature with the bank's domain, so in theory, this mail server was authorized to send this email on behalf of the bank. I have no idea if the receiving mail server checked the DKIM signature for validity though, and checking it manually is an exercise for another day.
We now have three (3) different domains associated with this email that aren't immediately identifiable as belonging to the bank that supposedly sent it: the one that sent the email, the one that hosts the images, and the one to which the links point. The only place the bank's domain appears is in the easily forged 'from' address and the potentially unverified DKIM signature. It's time to do some digging and see who's behind these domains.
Identifying the first two (2) are easy. Putting sparkpostmail.com into a web browser displays the 'report abuse' page for SparkPost, an email platform that claims to be 'the world's largest and most reliable email sender, delivering nearly 40% of all commercial email'. Browsing to getblueshift.com displays the homepage of Blueshift, a content delivery network. However, attempting to browse csgipe.com reveals that there is no webserver at that address, so some more digging is required.
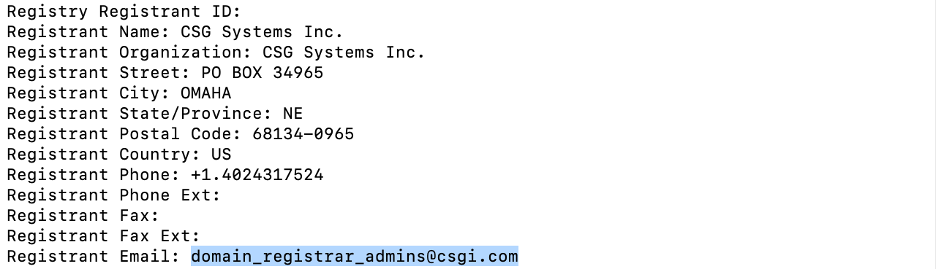
A quick WHOIS search on the csgipe.com domain reveals that it is registered to a company called CSG Systems Inc. and the registrant email is at the csgi.com domain. Browsing to csgi.com displays a homepage stating 'CSG delivers innovative customer engagement solutions that help you acquire, monetize, engage and retain customers.'
The Realization: Marketing Tools are Efficient but Need to be Checked
The services these three (3) domains offer reveal what is likely happening here: A major national bank is using the same ecosystem of commercial bulk email, content delivery, and tracking services for both their marketing emails and important fraud alert emails. This practice makes the resulting messages indistinguishable from commercial bulk email and very similar to targeted phishing emails. My suspicions were confirmed when I finally picked up the phone, called the number on the back of my card, and was immediately asked if I made the same charge described in the email.
Using commercial 'marketing' systems in this manner may be a matter of convenience for the sender, but it may also be a tactic to avoid problems with their own email servers. (A large bank likely sends an enormous volume of fraud alerts per day and sending too much bulk email could impact a mail server's sending reputation.) This could result in the mail servers getting blacklisted and critical person-to-person emails passing through those servers getting blocked by receiving servers. Routing email through a third-party service shifts this risk. Still, there are better ways to do this without putting up almost all the red flags that indicate phishing.
The Right Way: Keep it Simple and Avoid Links
I've been an Information Security professional for 20 years, I've run training on identifying and avoiding phishing emails, and I've crafted mock phishing emails during penetration tests. I also have the technical skills to perform the analysis described above. If it takes me this much effort to tell the difference between a legitimate and fraudulent email, there is no hope for the great masses of less technically savvy users. Organizations need to do better than this. To do otherwise is actively training users to fall for phishing emails.
Phishing awareness training focuses on a few key points that nearly anyone should be able to understand:
- Check the sender address to make sure it comes from the expected domain
- Don't download attachments
- Check the links to make sure they point to the expected domain prior to clicking on them
- Don't provide sensitive information (e.g., passwords or credit card numbers) to any website you access via a link in an email
The best way to make it evident that your email is not a phishing attempt is to keep it simple and eliminate the links completely. I would have immediately taken my email seriously if, instead of giant 'yes' and 'no' graphical buttons with third-party links, it had a single line of text that said: 'Call the number on the back of your credit card to confirm this transaction.' Since the entire goal of a phishing email is to trick the user into navigating to a website or opening a file that they have provided, we can short-circuit this process by referring the user to a known-good source of information instead.
Sometimes links in emails may be necessary, e.g., you don't have a known good source of information to refer recipients to. Your email had better look completely legitimate if your organization sends a message asking someone to click a link and input personal information into a website. The key point is to send the email from a domain and have links that go to a domain that is easily recognizable as belonging to your organization. If your organization's main domain is example.com, the links should go to something at example.com or at least a subdomain like fraud.example.com. It should not be a variation of the domain name like examplefraud.com, as it's too easy for someone else to pick up a domain similar to your own for a few bucks and use it to spoof your real website.
Many organizations struggle with phishing, both when they get breached because of their own internal users getting phished and when customers get phished and give away credentials or other sensitive information that can be used for fraud. Most organizations have some sort of phishing awareness program, and this training is not just for recipients of emails. It's just as important for personnel responsible for sending emails to take those lessons to heart to avoid sending a questionable message that could confuse recipients and make them more likely to fall for phishing emails in the future.