Theft From Online Shopping Carts - Past and Present

Past
Circa 2007, during a penetration test, I encountered an online shopping cart that exposed a variable containing a product's price and it allowed for manipulation to lower the cart's total. In early 2008, research was conducted to answer the question - just how many carts are vulnerable to such a trivial hack? At the time, PayPal had a Solutions Directory that listed online shopping carts that integrated with them for payment. Since this was an easy way to identify a large number of carts, a list of 136 carts was made and research began.
Of the 136 carts, only 123 offered an online demo, with 23 of them passing a price and 100 of them not displaying that behavior. That translates to roughly 18.7% of them being vulnerable in 2008. The test did not attempt a check out process, it was limited to online demos using the "add to cart" or "update cart" functionality only. This simple research with proposed modifications was rejected as a Defcon talk, so resurfacing the data 12 years later could make for an interesting topic.
Present
A lot has changed in the security industry since 2008, and education and awareness are much more visible. Today's shopping carts do not usually pass the price around directly, but there are other ways in which we manipulate them in our favor during penetration tests.
Typical outcomes in today's carts include item price modification, discounts with coupon codes, order total manipulation, and alterations for free shipping. Many attacks are the result of an insecure direct object reference (IDOR) vulnerability, where an internal implementation object, such as a price variable, is exposed to the user/client and can be changed with the new value accepted by the server, resulting in behavior unintended by the developer.
The main ways in which we typically manipulate online shopping carts or transactions in our favor are:
- Simple price change (not common anymore)
- Negative quantities
- Partial quantities
- Add-ons/extra options
- Coupon codes
- Race conditions
- Gift card theft
Simple Price Change
The simple price change is when the price is exposed and can be changed, with the value accepted by the server. This is very uncommon in 2020. Most shopping carts simply pass a product ID and a quantity variable to perform cart functions.
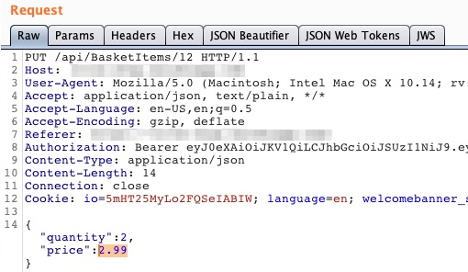
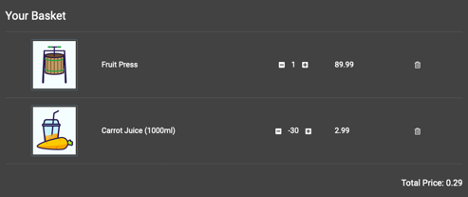
Negative Quantities
Negative quantities are a gamble as they require a product in your cart to have a negative price in conjunction with a product displaying a positive price. If you add one item that you want at $99.99 and another that you may or may not want that is priced at $199.99, but with a quantity of negative one, the cart total would be negative $100.00 with a total quantity of two total items in the cart. What happens if the checkout process is attempted with a pre-paid credit card? Does the merchant credit your card with $100? There is only one way to find out!
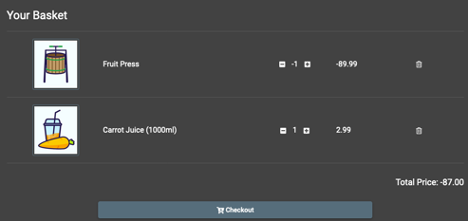
Most often, carts will require the total to be a positive number and not less than or equal to zero. This doesn't rule out free orders or those with zero totals, but it's worth a try! Typically, the positive amount item is the item you want, and the negative quantity item is the one you do not want; however, it is worth noting that you should likely choose two products that you wouldn't mind having delivered. It's very important to note that TrustedSec discusses and obtains rules of engagement from clients before any shopping cart testing is performed. We often request permission to attempt to steal up to $50 worth of goods from the client as a proof of concept. The closer you can make the difference between the positive and negative quantity items in your cart to $0.01, the better. Who wouldn't want two items for a penny? A prepaid credit card with $20 or less is used in case the fraudulent attempt is caught and a full charge is made to the card. Since we have $20 or less available on the card, the full charge would likely be unauthorized and declined.
Warning! This and many of these scenarios are risky to test in production environments, as they will likely have unexpected outcomes. For example, if TrustedSec's client is an auto glass dealer and the installation is always handled locally by a repair shop with an appointment, the client (or vendor in this example) may initiate a warehouse pick ticket to send auto glass to a repair shop for installation as soon as the order is created, despite batch credit card processing at the end of each day. Will the client's systems process the negative quantity? Will the warehouse pick ticket show the negative quantity? Will the warehouse worker notice it or fulfill the order with both the positive and negative quantity items anyway?
By the time the credit card is rejected or the fraudulent order is created, glass might have been picked from the warehouse, loaded on a truck, and on its way to the destination! The local shop is often billed for that and in some cases would be stuck with the purchase. Be careful with shopping cart attacks and always verify with your client before attempting malicious orders/purchases! In TrustedSec's experience, all items are included provided the prices are not exorbitant. Since we use $50 as a maximum, our attempts often go unnoticed and do not trip fraud alerts.
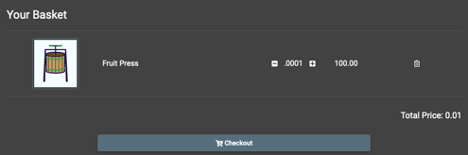
Partial Quantities
Another application assessment for one of TrustedSec's clients involved developers with some security education in their background. The affected site's shopping cart did not allow negative quantities. I attempted to add an item priced at $100 to the cart with a .0001 quantity, which resulted in a $0.01 cart total. Partial or fractional quantities are another avenue for an attack that should be checked.
Add-Ons/Extra Options
Another client was in the food business that allowed for online ordering. This case was interesting, as the typical aforementioned issues were not present in the custom shopping cart implementation. This client's successful attack avenue was the result of tampering with extra options for items. For example, if a pizza is ordered online, one could choose extra cheese for an upcharge. This particular situation allowed for adding a food item (a hamburger for example) to the cart, and then selecting from a large list of options. The add-on options were accepted as negative quantities server-side, while the hamburger itself was not. This made things interesting, as a hamburger was added to the cart with a negative one quantity of every topping possible. The $8 hamburger was now priced at under $1 with all of the negative condiment/add-on quantities. When the TrustedSec consultant went to the location to pick up the food, the employees were very confused since the receipt was very long, displaying a negative one for each topping printed. The employees didn't understand what happened and allowed the food to be taken, not noticing the very small total at the bottom that was prepaid online. A little social engineering in person ('playing dumb') went a long way. Of course, this was all done with the client's permission.
Coupon Codes
Most online shopping carts offer the merchant a way to use promotional coupons for free shipping, a percentage off of an order, or other discounts. It has been observed that while many login pages throttle or block multiple brute-force attempts, most online carts do not have brute-force protections in place for repeatedly attempting to apply coupon codes. With BurpSuite's Intruder or some custom scripting, it is trivial to run a wordlist against such functionality. Typical variations include holiday-related words and percentages off such as "CHRISTMAS20," giving 20% off an order at Christmas time. Others include words for numbers such as "FIVEOFF" for $5 or 5% off, or sometimes more direct promotions, like "FREESHIPPING" for free shipping on an order. It is pretty easy to create a fuzz list and prepend and append words to get lucky.
Race Conditions
The last way in which we've taken advantage of online shopping carts is one of the most difficult to identify and perform. Oftentimes, online carts will ask for a zip code or address and then calculate shipping costs. Some carts "normalize" addresses to a USPS accepted format to ensure delivery. In this client's shopping cart, the shipping was free if it could not complete the address verification before the checkout was presented to the user. Basically, if you click the browser's back button and then click the checkout button and do that rapidly, eventually the price would drop slightly. This was possible because shipping was not included. This is easier to test when scripted, but an edge case like this is often overlooked by many penetration testers.
Gift Card Theft
The final way in which TrustedSec has been able to manipulate online shopping carts and their check out process in our favor is through certain gift card payment attacks. Similar to brute-forcing coupon codes, many gift cards have a number and an associated pin which is subject to attack. Gift card resale is a large market online. If a gift card's number is visible in online auctions or sites or even in a retail store, it can be easily obtained by attackers. From here, only one factor is needed to see the format of the secondary factor, the pin. For one client, the pin that was checked was a small key space since it contained only four digits of validation. The shopping cart also did not prevent any sort of brute-force attacks. A quick search of eBay and 10,000 or less requests resulted in successful theft of someone's unused gift card credit.
Conclusion
The world of online shopping carts has changed a lot in the last 10-15 years, however, TrustedSec consultants are still successfully taking advantage of them regularly. Hopefully, this blog post shed some light on the ways in which criminals might be creatively taking advantage of your organization in ways you may have not imagined.