Top 5 Things That Will Land an Attacker in the Azure Cloud

1. Misconfigured Cloud Infrastructure
What type of misconfigurations can exist in a cloud infrastructure?
Vulnerable front-facing webservers, unpatched appliances, and storage accounts allowing anonymous public access are just a few examples of common infrastructure misconfigurations in cloud environments.
How can these services translate into an attacker gaining access to my cloud?
Storage accounts can hold a wide range of data types, including documents that contain plaintext credentials, secrets stored in JSON or XML format, and private keys.
Vulnerable web servers can contain an array of different footholds. If an attacker can gain shell access, it could allow pivoting to your internal network if the webserver is configured to do so. The server could also be hosted within a docker container. Docker containers can be configured with environment variables that may expose credentials and client secrets in plaintext, which could also allow a foothold into your cloud environment.
2. Phishing
Is your organization protected with MFA? Many enterprises are not using phishing-resistant forms of MFA. Under certain conditions, attackers can be granted cloud access by phishing and replaying an access token that can bypass MFA.
The following phishing message could convince an unsuspecting user to inadvertently give an attacker cloud access.
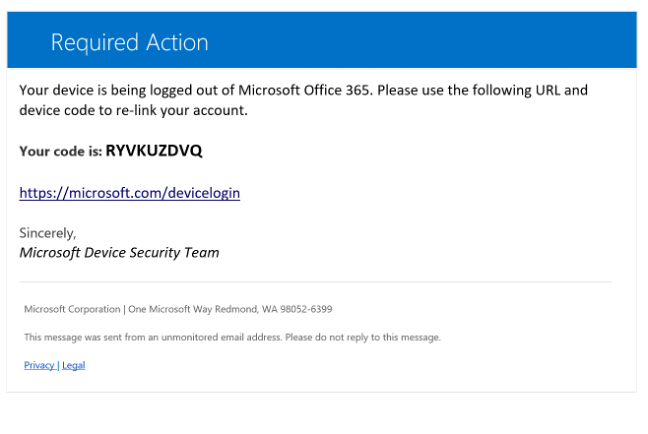
According to the Microsoft Digital Defense Report in 2021, phishing was responsible for 70% of data breaches.
3. Weak Credentials/Credential Reuse
Winter2023! is an example of a weak password because it contains a season and a year. In cases where an enterprise requires frequent password changes, these types of passwords are more common because they are very easy for an end-user to remember. This password policy can result in users making poor decisions when creating passwords.
Do you have a password compliance policy that requires an industry standard of 14 characters or more? Wintertime2023! is another example of a weak password that technically meets that password policy requirement. Of course, weak passwords don't have to incorporate seasons or months—if your enterprise name is Widgets Inc, then another example of a weak password would be Widgets2023!. Unfortunately, these types of password combinations are very common for us to see during a cloud penetration test.
Credential reuse is also common when cross-referencing public breach data. Services such as DeHashed can offer valuable insight into how end-users are making decisions on passwords. It’s also worth spraying cloud infrastructure with existing exposed passwords from past data breaches to gain initial entry.
4. Weak/No MFA
Although MFA adds a barrier to entry, its configuration may not stop an attacker from gaining initial access into a cloud environment. For example, if an enterprise is using MFA push notifications, the attacker may simply bombard the end-user with push notifications until the end-user accepts. If this happens, the attacker may exfiltrate emails, view Teams conversations, and steal sensitive documents stored in SharePoint Online. If end-users are storing plaintext passwords in SharePoint, an attacker could further pivot into your cloud infrastructure.
Unfortunately, security defaults were not automatically enabled unless the Azure tenant was created on or after October 22, 2019. This can present some security gaps in MFA adoption for organizations that are on the free tier of Azure AD. Customers who pay for Azure AD licensing have additional setup decisions to make in Conditional Access in order to turn on MFA for all end-users. Back in February 2022 Microsoft disclosed that only 22% of Azure AD customers had MFA enabled. Deploying MFA and ensuring all users are registered can be a massive undertaking. Several components should be considered when adopting MFA:
- Communication to employees about registering
- Types of MFA allowed (SMS, codes, number matching authentication, FIDO2)
- Auditing employee registration
- Strategies for securing accounts such as service accounts that won’t use MFA
- Controlling security information and preventing unsecure MFA registration (using Temporary Access Pass)
- Designing Conditional Access strategies for identity and MFA usage
Even after you adopt MFA, end-users can still fail to register. This can happen if you have staff who never authenticate to cloud resources outside of a trusted location and you have Conditional Access policies that don’t require MFA to be used within those trusted boundaries.
5. Insider Activity
Insider activity can be grouped into two (2) categories, intentional and unintentional. Intentional insider activity is where an employee may be selling access to cloud infrastructure in exchange for money on underground or otherwise illegitimate websites. It’s usually financially motivated.
Unintentional insider activity is where an employee accidentally exposes credentials to a cloud resource using a source code repository that is open to the public such as GitHub or GitLab. Depending on the resource, an attacker can establish a potential foothold with minimal effort.
When looking at this type of cloud threat, a few questions should be considered:
- Is my logging solution going to alert me when someone logs in from a foreign country?
- Is it going to alert me when someone elevates privileges to existing subscriptions in my tenant?
- Will I get alerted if there are firewall changes in my cloud environment?
- If someone starts issuing Azure VM run commands, can my SOC detect that type of activity?
Cloud monitoring gaps can allow insider activity to go undetected and enterprises can lose visibility to remediate these types of issues in a timely manner before data loss occurs.
Conclusion
Unprotected cloud environments can pose significant threats to your company reputation, data, and applications. Your cloud posture can be subject to many changes each year, and the only way to protect your cloud investment is to have your environment routinely tested and audited. It is essential for enterprises to have robust security measures and access controls in the cloud to decrease your risk and mitigate potential harm.