Our team
With our expertise, technical skills, and ethical character, we’ll help you secure what’s most important to you. Interested in a career at TrustedSec? Check out our careers page below for job openings!

Meet the experts
Our exceptional team of security consultants and advisors are ready to tackle your information security challenges and deliver practical results.

Jessica Archer
Director of Sales

Jason Ashton
Practice Lead, Training & Mentorship

Alex Ball
Senior Research Analyst

Shaun Bell
Senior Systems Administrator

Brian Berg
Senior Security Consultant

Scot Berner
Principal Security Consultant

Zach Bevilacqua
Security Consultant

Scott Blake
Senior Security Consultant

Chris Boesch
VP, Sales and Marketing

Justin Bollinger
Principal Security Consultant

Michael Bond
Security Consultant

Martin Bos
CSO & VP of Consulting Services

David Boyd
Senior Security Consultant

Ryan Boyle
Security Consultant

Luke Bremer
Senior Security Consultant II

Rockie Brockway
Director of Advisory Innovation

Suzanne Burdick
Director of Finance

Paul Burkeland
Practice Lead, Force Cloud Security

John Burnheimer
Senior Account Manager

Ryan Burnheimer
VP of Business Development

Chris Camejo
Director of Advisory Services

Brian Cantrell
Chief Operating Officer

Dylan Carr
Junior Systems Administrator

Ricky Christoff
Junior Systems Administrator

Kevin Clark
Senior Security Consultant

Christine Cline
Engagement Manager

Brandon Colley
Senior Security Consultant

Lakeith Collins
Senior Security Consultant

Adam Compton
Principal Security Consultant
Austin Coontz
Security Consultant

Art Cooper
Principal Security Consultant

Chuck Cothren
Senior Security Consultant

Jason Crawford
Senior Security Consultant

Edwin David
Senior Security Consultant

Julie Daymut
Senior Copy Editor

Josh Deen
Security Consultant

Kim DeSimone
Director of HR

Nick Doerner
Security Consultant

Philip DuBois
Senior Security Consultant

Danny Dubree
Security Consultant

Justin Elze
CTO, Director of Research

Mike Felch
Principal Security Consultant

Caroline Fenstermacher
Security Consultant

Gary Fetters
Senior Copy Editor

Andrea Floro
Senior Account Manager

Eric Fry
Senior Account Manager
Linus Garin
Security Consultant

Fatima Ghani
Security Consultant

Alex Hamerstone
Advisory Solutions Director

Shane Hartman
Principal Security Consultant

Kevin Haubris
Senior Research Analyst

Dylan Isaacs
Account Manager

Aaron James
Senior Security Consultant

Kurt Jensen
Senior Compliance Consultant

Alex Kah
Senior Systems Administrator

Misty Kaiser
Accounting Clerk

Travis Kaun
Senior Security Consultant

David Kennedy
Founder & CEO

Erin Kennedy
Vice President of Finance

Drew Kirkpatrick
Principal Security Consultant

Paul Koblitz
Managing Director of Technical Services

Hans Lakhan
Principal Security Consultant

Jason Lang
Practice Lead, Targeted Operations

Melvin Langvik
Senior Security Consultant

Ryan Leese
Senior Security Consultant

Andrew Lentz
Security Consultant

Katie Link
Senior Engagement Coordinator

Sam Link
Principal Security Consultant

Jack Love
Senior Engagement Coordinator

Ryan Macfarlane
Practice Lead, Incident Response

Justin Mahon
Security Consultant

Roza Maille
Content & Community Manager

Daniel Mark
Senior Account Manager

Patrick "Lilly" Mayo
Senior Security Consultant

Steve Maxwell
Senior Security Consultant

Brandon McGrath
Senior Security Consultant

Jared McWherter
Practice Lead, Maturity

Sean Metcalf
Identity Security Architect

Thomas Millar
Senior Security Consultant

Jim Mitchell
Director of Marketing

Oddvar Moe
Principal Security Consultant

Kurt Muhl
Senior Security Consultant

Megan Nilsen
Practice Lead, Attack Simulation and Detection, Tactical Awareness & Countermeasures (TAC)

Sarah Norris
Senior Security Consultant

Scott Nusbaum
Principal Research Analyst

Mike Owens
Practice Lead, Remediation

Tina Parker
Team Lead, Engagement Management

Christopher Paschen
Research Practice Lead

Ron Pazo
Security Consultant

Carlos Perez
Director of Security Intelligence

Jeff Pergal
Technical Solutions Director

Costa Petros
Senior Security Consultant

Whitney Phillips
Senior Security Consultant

Dominick Pissini
Associate Security Consultant
Lee Quinton
Practice Lead, Compliance

Esteban Rodriguez
Senior Security Consultant

Luis Rodriguez
Security Consultant

Phil Rowland
Practice Lead, Remediation Services

Alex Sauer
Marketing Coordinator

Lou Scicchitano
Senior Security Consultant

Kelsey Segrue
Senior Security Consultant

Steph Saunders
Senior Security Consultant

Paul Sems
Managing Director of Remediation Services

Brandi Shaffer
Team Lead, Quality Assurance

Jessica Sheneman
Design Project Manager

Rob Simon
Practice Lead, Mobile and Hardware Security
Mike Spitzer
Senior Security Engineer

Larry Spohn
Practice Lead, Force

Travis Steadman
Security Consultant

Joe Sullivan
Senior Security Consultant

Lumi Taiwo
Senior Security Consultant

David Thompson
Senior Account Manager

Nicole Tsakoumagos
Senior Copy Editor

Skyler Tuter
Senior Security Consultant

Geoff Walton
Practice Lead, Application Security

Jonathan White
Senior Security Consultant

Scott White
Director of Software Security

James Williams
Senior Security Consultant

Esra Yagan
Senior Account Manager

Charles Yost
Senior Software Engineer
Making a difference in security
We set out to change security by assembling the most technically advanced team of consultants and advisors.
“Our collaborative culture and reputation has attracted the most passionate, highly skilled professionals in the industry. It's incredible to see that the work we are doing is changing the industry.”Larry SpohnPractice Lead, Force

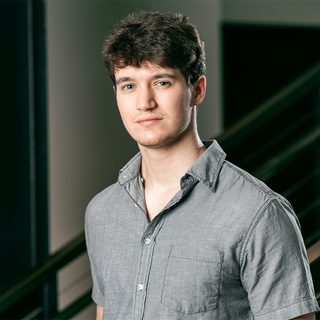
Larry Spohn
Practice Lead, ForceLarry Spohn is a highly experienced security consultant with over 20 years of experience in the industry and a proven track record of success in assessing and improving the security posture of organizations of all sizes. Larry is not only a skilled technical analyst with a deep understanding of security threats and vulnerabilities, but he is also an excellent communicator and trainer who is adept at conveying complex security concepts to both technical and non-technical audiences.
“For me it’s more of a life choice and a passion than anything else. I don’t consider it work at all. I get to work with some of the best, most talented hackers in the world, literally.”Jason LangPractice Lead, Targeted Operations

Jason Lang
Practice Lead, Targeted OperationsWith over 15 years of industry experience, Jason Lang has worked in both offensive and defensive roles. Before switching to red teaming, he spent 8 years working as a technical Security Architect for a Fortune 500 company, specializing in Active Directory and .Net/database development. After several years of penetration testing and red teaming, he now manages the Targeted Operations practice at TrustedSec.
“It's an incredible, collaborative environment where I can rely on anyone for support, and that's truly priceless.”Martin BosCSO, VP of Consulting Services

Martin Bos
CSO, VP of Consulting ServicesMartin works extensively with clients to help understand where and why their defenses failed and, more importantly, how to remediate the issues. For this reason, Martin is passionate about testing the security posture of organizations with all of the defenses and security controls in place. While working in the security field, Martin has conducted penetration testing against a large number of Fortune 500 companies in varying business verticals such as financial institutions, retail chains, casinos, manufacturing, and education.
Learn more about our services from an expert.
Let our experts tailor solutions to your security challenges.